mirror of
https://github.com/openfaas/faas.git
synced 2025-06-08 16:26:47 +00:00
Remove sample-functions in favour of newer examples
Signed-off-by: Alex Ellis (OpenFaaS Ltd) <alex@openfaas.com>
This commit is contained in:
parent
1ee7db994c
commit
40bb3581b7
@ -1,15 +0,0 @@
|
||||
FROM --platform=${TARGETPLATFORM:-linux/amd64} ghcr.io/openfaas/classic-watchdog:0.1.4 as watchdog
|
||||
|
||||
FROM --platform=${TARGETPLATFORM:-linux/amd64} alpine:3.16.0
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
# Populate example here
|
||||
# ENV fprocess="wc -l"
|
||||
|
||||
RUN addgroup -g 1000 -S app && adduser -u 1000 -S app -G app
|
||||
USER 1000
|
||||
|
||||
HEALTHCHECK --interval=5s CMD [ -e /tmp/.lock ] || exit 1
|
||||
CMD ["fwatchdog"]
|
||||
@ -1,7 +0,0 @@
|
||||
## AlpineFunction
|
||||
|
||||
This is a base image for Alpine Linux which already has the watchdog added and configured with a healthcheck.
|
||||
|
||||
This image is published on the Docker hub as `functions/alpine:latest`.
|
||||
|
||||
In order to deploy it - make sure you specify an "fprocess" value at runtime i.e. `sha512sum` or `wc -l`. See the docker-compose.yml file for more details on usage.
|
||||
@ -1,3 +0,0 @@
|
||||
#!/bin/sh
|
||||
|
||||
docker build -f Dockerfile.armhf -t functions/alpine:latest-armhf .
|
||||
@ -1,7 +0,0 @@
|
||||
### Api-Key-Protected sample
|
||||
|
||||
Please see [apikey-secret](../apikey-secret/README.md)
|
||||
|
||||
See the [secure secret management guide](../../guide/secure_secret_management.md) for instructions on how to use this function.
|
||||
|
||||
When calling via the gateway pass the additional header "X-Api-Key", if it matches the `secret_api_key` value then the function will give access, otherwise access denied.
|
||||
@ -1,19 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM artemklevtsov/r-alpine:latest
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
WORKDIR /application/
|
||||
|
||||
COPY handler.R .
|
||||
|
||||
ENV fprocess="Rscript handler.R"
|
||||
|
||||
RUN addgroup -g 1000 -S app && adduser -u 1000 -S app -G app
|
||||
USER 1000
|
||||
|
||||
HEALTHCHECK --interval=1s CMD [ -e /tmp/.lock ] || exit 1
|
||||
|
||||
CMD ["fwatchdog"]
|
||||
@ -1,42 +0,0 @@
|
||||
---
|
||||
title: "BaseFunction for R"
|
||||
output: github_document
|
||||
---
|
||||
|
||||
```{r setup, include=FALSE}
|
||||
knitr::opts_chunk$set(echo = TRUE)
|
||||
```
|
||||
|
||||
Use this OpenFaaS function using R.
|
||||
|
||||
**Deploy the base R function**
|
||||
|
||||
(Make sure you have already deployed OpenFaaS with ./deploy_stack.sh in the root of this Github repository.
|
||||
|
||||
* Option 1 - click *Create a new function* on the FaaS UI
|
||||
|
||||
* Option 2 - use the [faas-cli](https://github.com/openfaas/faas-cli/) (experimental)
|
||||
|
||||
```
|
||||
# curl -sSL https://get.openfaas.com | sudo sh
|
||||
|
||||
# faas-cli -action=deploy -image=functions/base:R-3.4.1-alpine -name=baser
|
||||
200 OK
|
||||
URL: http://localhost:8080/function/baser
|
||||
```
|
||||
|
||||
**Say Hi with input**
|
||||
|
||||
`curl` is good to test function.
|
||||
|
||||
```
|
||||
$ curl http://localhost:8080/function/baser -d "test"
|
||||
```
|
||||
|
||||
**Customize the transformation**
|
||||
|
||||
If you want to customise the transformation then edit the Dockerfile or the fprocess variable and create a new function.
|
||||
|
||||
**Remove the function**
|
||||
|
||||
You can remove the function with `docker service rm baser`.
|
||||
@ -1,34 +0,0 @@
|
||||
BaseFunction for R
|
||||
================
|
||||
|
||||
Use this FaaS function using R.
|
||||
|
||||
**Deploy the base R function**
|
||||
|
||||
(Make sure you have already deployed FaaS with ./deploy\_stack.sh in the root of this Github repository.
|
||||
|
||||
- Option 1 - click *Create a new function* on the FaaS UI
|
||||
|
||||
- Option 2 - use the [faas-cli](https://github.com/openfaas/faas-cli/) (experimental)
|
||||
|
||||
<!-- -->
|
||||
|
||||
# curl -sSL https://get.openfaas.com | sudo sh
|
||||
|
||||
# faas-cli -action=deploy -image=functions/base:R-3.4.1-alpine -name=baser
|
||||
200 OK
|
||||
URL: http://localhost:8080/function/baser
|
||||
|
||||
**Say Hi with input**
|
||||
|
||||
`curl` is good to test function.
|
||||
|
||||
$ curl http://localhost:8080/function/baser -d "test"
|
||||
|
||||
**Customize the transformation**
|
||||
|
||||
If you want to customise the transformation then edit the Dockerfile or the fprocess variable and create a new function.
|
||||
|
||||
**Remove the function**
|
||||
|
||||
You can remove the function with `docker service rm baser`.
|
||||
@ -1,5 +0,0 @@
|
||||
#!/bin/sh
|
||||
|
||||
echo "Building functions/base:R-3.4.1-alpine"
|
||||
docker build -t functions/base:R-3.4.1-alpine .
|
||||
|
||||
@ -1,7 +0,0 @@
|
||||
#!/usr/bin/env Rscript
|
||||
|
||||
f <- file("stdin")
|
||||
open(f)
|
||||
line<-readLines(f, n=1, warn = FALSE)
|
||||
|
||||
write(paste0("Hi ", line), stderr())
|
||||
@ -1,16 +0,0 @@
|
||||
## Base function examples
|
||||
|
||||
Examples of base functions are provided here.
|
||||
|
||||
Each one will read the request from the watchdog then print it back resulting in an HTTP 200.
|
||||
|
||||
| Language | Docker image | Notes |
|
||||
|------------------------|-----------------------------------------|----------------------------------------|
|
||||
| Node.js | functions/base:node-6.9.1-alpine | Node.js built on Alpine Linux |
|
||||
| Coffeescript | functions/base:node-6.9.1-alpine | Coffeescript/Nodejs built on Alpine Linux |
|
||||
| Golang | functions/base:golang-1.7.5-alpine | Golang compiled on Alpine Linux |
|
||||
| Python | functions/base:python-2.7-alpine | Python 2.7 built on Alpine Linux |
|
||||
| Java | functions/base:openjdk-8u121-jdk-alpine | OpenJDK built on Alpine Linux |
|
||||
| Dotnet Core | functions/base:dotnet-sdk | Microsoft dotnet core SDK |
|
||||
| Busybox / shell | functions/alpine:latest | Busybox contains useful binaries which can be turned into a FaaS function such as `sha512sum` or `cat` |
|
||||
| R | functions/base:R-3.4.1-alpine | R lang ready on Alpine Linux |
|
||||
@ -1,17 +0,0 @@
|
||||
FROM toricls/gnucobol:latest
|
||||
|
||||
RUN apt-get update && apt-get install -y curl \
|
||||
&& curl -sL https://github.com/openfaas/faas/releases/download/0.13.0/fwatchdog > /usr/bin/fwatchdog \
|
||||
&& chmod +x /usr/bin/fwatchdog \
|
||||
&& rm -rf /var/lib/apt/lists/* /tmp/* /var/tmp/*
|
||||
|
||||
WORKDIR /root/
|
||||
|
||||
COPY handler.cob .
|
||||
RUN cobc -x handler.cob
|
||||
ENV fprocess="./handler"
|
||||
|
||||
HEALTHCHECK --interval=1s CMD [ -e /tmp/.lock ] || exit 1
|
||||
|
||||
CMD ["fwatchdog"]
|
||||
|
||||
@ -1,8 +0,0 @@
|
||||
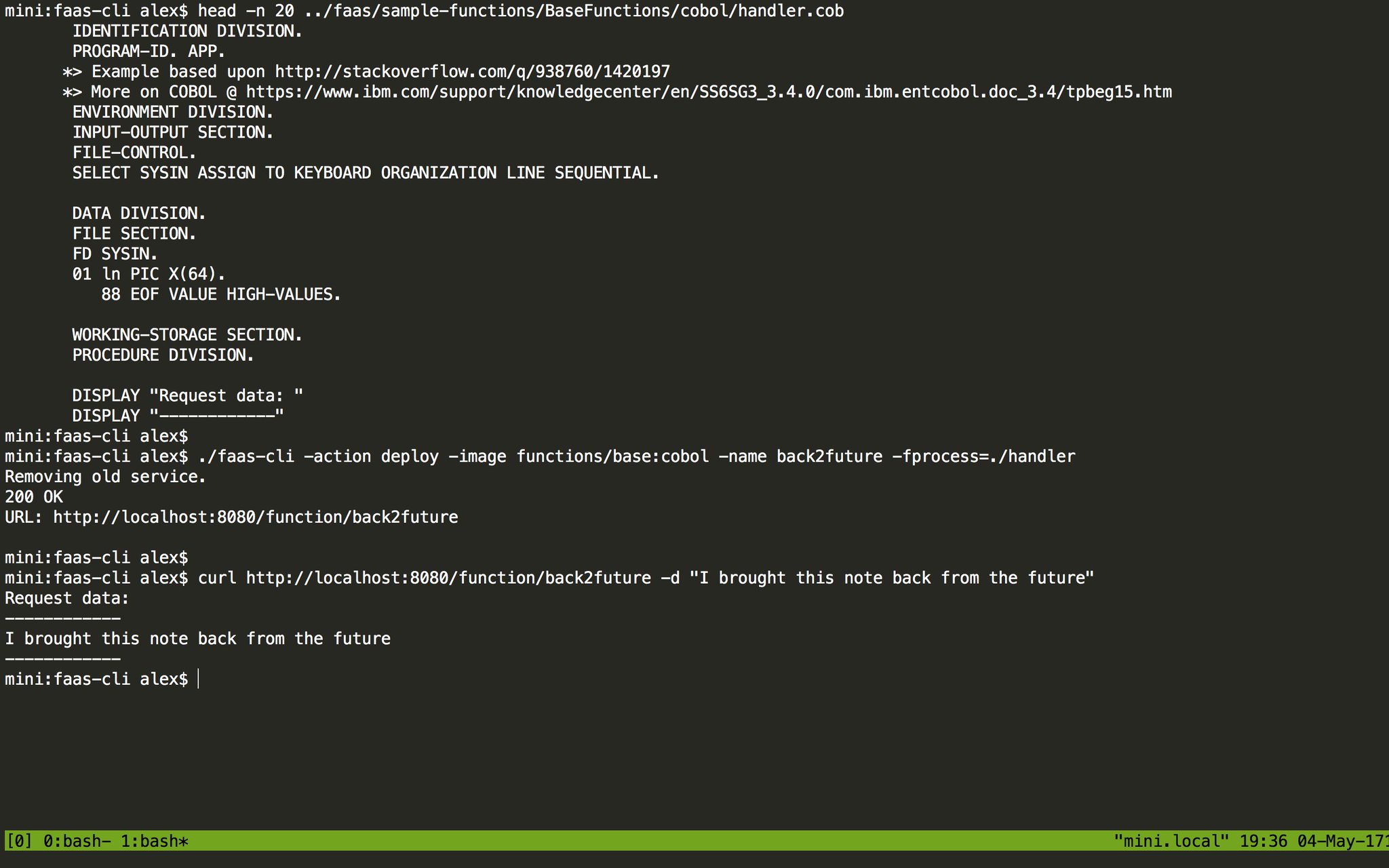
GNUCobol
|
||||
=========
|
||||
|
||||
Any binary can become a FaaS process, even Cobol through GNUCobol.
|
||||
|
||||
Here's an example of deploying this base function to FaaS which reads from stdin (called SYSIN in Cobol) and prints it to the screen.
|
||||
|
||||
|
||||
@ -1,4 +0,0 @@
|
||||
#!/bin/sh
|
||||
|
||||
echo "Building functions/base:cobol"
|
||||
docker build -t functions/base:cobol .
|
||||
@ -1,38 +0,0 @@
|
||||
IDENTIFICATION DIVISION.
|
||||
PROGRAM-ID. APP.
|
||||
*> Example based upon http://stackoverflow.com/q/938760/1420197
|
||||
*> More on COBOL @ https://www.ibm.com/support/knowledgecenter/en/SS6SG3_3.4.0/com.ibm.entcobol.doc_3.4/tpbeg15.htm
|
||||
ENVIRONMENT DIVISION.
|
||||
INPUT-OUTPUT SECTION.
|
||||
FILE-CONTROL.
|
||||
SELECT SYSIN ASSIGN TO KEYBOARD ORGANIZATION LINE SEQUENTIAL.
|
||||
|
||||
DATA DIVISION.
|
||||
FILE SECTION.
|
||||
FD SYSIN.
|
||||
01 ln PIC X(64).
|
||||
88 EOF VALUE HIGH-VALUES.
|
||||
|
||||
WORKING-STORAGE SECTION.
|
||||
PROCEDURE DIVISION.
|
||||
|
||||
DISPLAY "Request data: "
|
||||
DISPLAY "------------"
|
||||
|
||||
OPEN INPUT SYSIN
|
||||
READ SYSIN
|
||||
AT END SET EOF TO TRUE
|
||||
END-READ
|
||||
PERFORM UNTIL EOF
|
||||
|
||||
|
||||
DISPLAY ln
|
||||
|
||||
READ SYSIN
|
||||
AT END SET EOF TO TRUE
|
||||
END-READ
|
||||
END-PERFORM
|
||||
CLOSE SYSIN
|
||||
|
||||
DISPLAY "------------"
|
||||
STOP RUN.
|
||||
@ -1,6 +0,0 @@
|
||||
IDENTIFICATION DIVISION.
|
||||
PROGRAM-ID. HELLO-WORLD.
|
||||
PROCEDURE DIVISION.
|
||||
DISPLAY 'FaaS running COBOL in a container!'.
|
||||
STOP RUN.
|
||||
|
||||
@ -1,23 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM node:6.9.1-alpine
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
WORKDIR /application/
|
||||
|
||||
COPY package.json .
|
||||
|
||||
RUN npm install -g coffee-script && \
|
||||
npm i
|
||||
|
||||
COPY handler.coffee .
|
||||
|
||||
ENV fprocess="coffee handler.coffee"
|
||||
|
||||
HEALTHCHECK --interval=1s CMD [ -e /tmp/.lock ] || exit 1
|
||||
|
||||
USER 1000
|
||||
|
||||
CMD ["fwatchdog"]
|
||||
@ -1,5 +0,0 @@
|
||||
#!/bin/sh
|
||||
|
||||
echo "Building functions/base:coffeescript-1.12-alpine"
|
||||
docker build -t functions/base:coffeescript-1.12-alpine .
|
||||
|
||||
@ -1,7 +0,0 @@
|
||||
getStdin = require 'get-stdin'
|
||||
|
||||
handler = (req) -> console.log req
|
||||
|
||||
getStdin()
|
||||
.then (val) -> handler val
|
||||
.catch (e) -> console.error e.stack
|
||||
@ -1,16 +0,0 @@
|
||||
{
|
||||
"name": "NodejsBase",
|
||||
"version": "1.0.0",
|
||||
"description": "",
|
||||
"main": "faas_index.js",
|
||||
"scripts": {
|
||||
"test": "echo \"Error: no test specified\" && exit 1"
|
||||
},
|
||||
"keywords": [],
|
||||
"author": "",
|
||||
"license": "ISC",
|
||||
"dependencies": {
|
||||
"coffeescript": "^1.12.4",
|
||||
"get-stdin": "^5.0.1"
|
||||
}
|
||||
}
|
||||
@ -1,21 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM mcr.microsoft.com/dotnet/core/sdk:2.1 as build
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
ENV DOTNET_CLI_TELEMETRY_OPTOUT 1
|
||||
|
||||
WORKDIR /application/
|
||||
COPY src src
|
||||
WORKDIR /application/src
|
||||
RUN dotnet restore
|
||||
RUN dotnet build
|
||||
|
||||
FROM build as runner
|
||||
RUN groupadd -g 1000 -r faas && useradd -r -g faas -u 1000 faas -m
|
||||
USER 1000
|
||||
ENV fprocess="dotnet ./bin/Debug/netcoreapp2.1/root.dll"
|
||||
EXPOSE 8080
|
||||
CMD ["fwatchdog"]
|
||||
@ -1,9 +0,0 @@
|
||||
# DnCore Example
|
||||
DotNet seems to have an issue where the following message can bee seen on STDOUT:
|
||||
```
|
||||
realpath(): Permission denied
|
||||
realpath(): Permission denied
|
||||
realpath(): Permission denied
|
||||
```
|
||||
|
||||
This messages can be ignored and the issue can be followed at: https://github.com/dotnet/core-setup/issues/4038
|
||||
@ -1,5 +0,0 @@
|
||||
bin/
|
||||
obj/
|
||||
.nuget/
|
||||
.dotnet/
|
||||
.templateengine/
|
||||
@ -1,25 +0,0 @@
|
||||
using System;
|
||||
using System.Text;
|
||||
|
||||
namespace root
|
||||
{
|
||||
class Program
|
||||
{
|
||||
private static string getStdin() {
|
||||
StringBuilder buffer = new StringBuilder();
|
||||
string s;
|
||||
while ((s = Console.ReadLine()) != null)
|
||||
{
|
||||
buffer.AppendLine(s);
|
||||
}
|
||||
return buffer.ToString();
|
||||
}
|
||||
|
||||
static void Main(string[] args)
|
||||
{
|
||||
string buffer = getStdin();
|
||||
|
||||
Console.WriteLine(buffer);
|
||||
}
|
||||
}
|
||||
}
|
||||
@ -1,8 +0,0 @@
|
||||
<Project Sdk="Microsoft.NET.Sdk">
|
||||
|
||||
<PropertyGroup>
|
||||
<OutputType>Exe</OutputType>
|
||||
<TargetFramework>netcoreapp2.1</TargetFramework>
|
||||
</PropertyGroup>
|
||||
|
||||
</Project>
|
||||
@ -1,23 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM golang:1.13-alpine
|
||||
ENV CGO_ENABLED=0
|
||||
|
||||
MAINTAINER alexellis2@gmail.com
|
||||
ENTRYPOINT []
|
||||
|
||||
WORKDIR /go/src/github.com/openfaas/faas/sample-functions/golang
|
||||
COPY . /go/src/github.com/openfaas/faas/sample-functions/golang
|
||||
|
||||
RUN go install
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
ENV fprocess "/go/bin/golang"
|
||||
HEALTHCHECK --interval=1s CMD [ -e /tmp/.lock ] || exit 1
|
||||
|
||||
RUN addgroup -g 1000 -S app && adduser -u 1000 -S app -G app
|
||||
USER 1000
|
||||
|
||||
CMD [ "fwatchdog"]
|
||||
@ -1,16 +0,0 @@
|
||||
FROM golang:1.9.7-windowsservercore
|
||||
MAINTAINER alexellis2@gmail.com
|
||||
ENTRYPOINT []
|
||||
|
||||
WORKDIR /go/src/github.com/openfaas/faas/sample-functions/golang
|
||||
COPY . /go/src/github.com/openfaas/faas/sample-functions/golang
|
||||
RUN go build
|
||||
|
||||
ADD https://github.com/openfaas/faas/releases/download/0.13.0/fwatchdog.exe /watchdog.exe
|
||||
|
||||
EXPOSE 8080
|
||||
ENV fprocess="golang.exe"
|
||||
|
||||
ENV suppress_lock="true"
|
||||
|
||||
CMD ["watchdog.exe"]
|
||||
@ -1,10 +0,0 @@
|
||||
BaseFunction for Golang
|
||||
=========================
|
||||
|
||||
You will find a Dockerfile for Linux and one for Windows so that you can run serverless functions in a mixed-OS swarm.
|
||||
|
||||
Dockerfile for Windows
|
||||
* [Dockerfile.win](https://github.com/openfaas/faas/blob/master/sample-functions/BaseFunctions/golang/Dockerfile.win)
|
||||
|
||||
This function reads STDIN then prints it back - you can use it to create an "echo service" or as a basis to write your own function.
|
||||
|
||||
@ -1,4 +0,0 @@
|
||||
#!/bin/sh
|
||||
|
||||
echo "Building functions/base:golang-1.7.5-alpine"
|
||||
docker build -t functions/base:golang-1.7.5-alpine .
|
||||
@ -1,16 +0,0 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"io/ioutil"
|
||||
"log"
|
||||
"os"
|
||||
)
|
||||
|
||||
func main() {
|
||||
input, err := ioutil.ReadAll(os.Stdin)
|
||||
if err != nil {
|
||||
log.Fatalf("Unable to read standard input: %s", err.Error())
|
||||
}
|
||||
fmt.Println(string(input))
|
||||
}
|
||||
@ -1 +0,0 @@
|
||||
*.class
|
||||
@ -1,21 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM openjdk:8u121-jdk-alpine
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
WORKDIR /application/
|
||||
|
||||
COPY Handler.java .
|
||||
RUN javac Handler.java
|
||||
|
||||
ENV fprocess="java Handler"
|
||||
|
||||
RUN addgroup -g 1000 -S app && adduser -u 1000 -S app -G app
|
||||
USER 1000
|
||||
|
||||
HEALTHCHECK --interval=1s CMD [ -e /tmp/.lock ] || exit 1
|
||||
|
||||
CMD ["fwatchdog"]
|
||||
|
||||
@ -1,30 +0,0 @@
|
||||
import java.io.BufferedReader;
|
||||
import java.io.IOException;
|
||||
import java.io.InputStreamReader;
|
||||
|
||||
public class Handler {
|
||||
|
||||
public static void main(String[] args) {
|
||||
try {
|
||||
|
||||
String input = readStdin();
|
||||
System.out.print(input);
|
||||
|
||||
} catch(IOException e) {
|
||||
e.printStackTrace();
|
||||
}
|
||||
}
|
||||
|
||||
private static String readStdin() throws IOException {
|
||||
BufferedReader br = new BufferedReader(new InputStreamReader(System.in));
|
||||
String input = "";
|
||||
while(true) {
|
||||
String line = br.readLine();
|
||||
if(line==null) {
|
||||
break;
|
||||
}
|
||||
input = input + line + "\n";
|
||||
}
|
||||
return input;
|
||||
}
|
||||
}
|
||||
@ -1,4 +0,0 @@
|
||||
#!/bin/sh
|
||||
|
||||
echo "Building functions/base:openjdk-8u121-jdk-alpine"
|
||||
docker build -t functions/base:openjdk-8u121-jdk-alpine .
|
||||
@ -1,22 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM node:6.9.1-alpine
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
WORKDIR /application/
|
||||
|
||||
COPY package.json .
|
||||
|
||||
RUN npm i
|
||||
COPY handler.js .
|
||||
|
||||
USER 1000
|
||||
|
||||
ENV fprocess="node handler.js"
|
||||
|
||||
HEALTHCHECK --interval=1s CMD [ -e /tmp/.lock ] || exit 1
|
||||
|
||||
CMD ["fwatchdog"]
|
||||
|
||||
@ -1,5 +0,0 @@
|
||||
#!/bin/sh
|
||||
|
||||
echo "Building functions/base:node-6.9.1-alpine"
|
||||
docker build -t functions/base:node-6.9.1-alpine .
|
||||
|
||||
@ -1,13 +0,0 @@
|
||||
"use strict"
|
||||
|
||||
let getStdin = require('get-stdin');
|
||||
|
||||
let handle = (req) => {
|
||||
console.log(req);
|
||||
};
|
||||
|
||||
getStdin().then(val => {
|
||||
handle(val);
|
||||
}).catch(e => {
|
||||
console.error(e.stack);
|
||||
});
|
||||
@ -1,15 +0,0 @@
|
||||
{
|
||||
"name": "NodejsBase",
|
||||
"version": "1.0.0",
|
||||
"description": "",
|
||||
"main": "faas_index.js",
|
||||
"scripts": {
|
||||
"test": "echo \"Error: no test specified\" && exit 1"
|
||||
},
|
||||
"keywords": [],
|
||||
"author": "",
|
||||
"license": "ISC",
|
||||
"dependencies": {
|
||||
"get-stdin": "^5.0.1"
|
||||
}
|
||||
}
|
||||
@ -1,20 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM python:2.7-alpine
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
WORKDIR /application/
|
||||
|
||||
COPY handler.py .
|
||||
|
||||
ENV fprocess="python handler.py"
|
||||
|
||||
RUN addgroup -g 1000 -S app && adduser -u 1000 -S app -G app
|
||||
USER 1000
|
||||
|
||||
HEALTHCHECK --interval=1s CMD [ -e /tmp/.lock ] || exit 1
|
||||
|
||||
CMD ["fwatchdog"]
|
||||
|
||||
@ -1,5 +0,0 @@
|
||||
#!/bin/sh
|
||||
|
||||
echo "Building functions/base:python-2.7-alpine"
|
||||
docker build -t functions/base:python-2.7-alpine .
|
||||
|
||||
@ -1,11 +0,0 @@
|
||||
import sys
|
||||
|
||||
def get_stdin():
|
||||
buf = ""
|
||||
for line in sys.stdin:
|
||||
buf = buf + line
|
||||
return buf
|
||||
|
||||
if __name__ == "__main__":
|
||||
st = get_stdin()
|
||||
print(st)
|
||||
3
sample-functions/CHelloWorld/.gitignore
vendored
3
sample-functions/CHelloWorld/.gitignore
vendored
@ -1,3 +0,0 @@
|
||||
template
|
||||
build
|
||||
master.zip
|
||||
@ -1,20 +0,0 @@
|
||||
Hello World in C
|
||||
===================
|
||||
|
||||
This is hello world in C using GCC and Alpine Linux.
|
||||
|
||||
It also makes use of a multi-stage build and a `scratch` container for the runtime.
|
||||
|
||||
```
|
||||
$ faas-cli build -f ./stack.yml
|
||||
```
|
||||
|
||||
If pushing to a remote registry change the name from `alexellis` to your own Hub account.
|
||||
|
||||
```
|
||||
$ faas-cli push -f ./stack.yml
|
||||
$ faas-cli deploy -f ./stack.yml
|
||||
```
|
||||
|
||||
Then invoke via `curl`, `faas-cli` or the UI.
|
||||
|
||||
@ -1,32 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM alpine:3.16.0 as builder
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
WORKDIR /application/
|
||||
|
||||
RUN addgroup -g 1000 -S app && adduser -u 1000 -S app -G app
|
||||
|
||||
RUN apk add --no-cache gcc \
|
||||
musl-dev
|
||||
COPY main.c .
|
||||
|
||||
RUN gcc main.c -static -o /main \
|
||||
&& chmod +x /main \
|
||||
&& /main
|
||||
|
||||
FROM scratch
|
||||
|
||||
COPY --from=builder /main /
|
||||
COPY --from=builder /usr/bin/fwatchdog /
|
||||
|
||||
ENV fprocess="/main"
|
||||
ENV suppress_lock=true
|
||||
|
||||
COPY --from=builder /etc/passwd /etc/passwd
|
||||
|
||||
USER 1000
|
||||
|
||||
CMD ["fwatchdog"]
|
||||
|
||||
@ -1,9 +0,0 @@
|
||||
#include<stdio.h>
|
||||
|
||||
int main() {
|
||||
|
||||
printf("Hello world\n");
|
||||
|
||||
return 0;
|
||||
}
|
||||
|
||||
@ -1,9 +0,0 @@
|
||||
provider:
|
||||
name: openfaas
|
||||
gateway: http://127.0.0.1:8080
|
||||
|
||||
functions:
|
||||
helloc:
|
||||
lang: Dockerfile
|
||||
handler: ./src
|
||||
image: alexellis/helloc:0.1
|
||||
@ -1,21 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM alpine:3.16.0 as ship
|
||||
RUN apk --update add nodejs npm
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
WORKDIR /application/
|
||||
|
||||
COPY package.json .
|
||||
COPY handler.js .
|
||||
COPY parser.js .
|
||||
COPY sample.json .
|
||||
|
||||
RUN npm i
|
||||
ENV fprocess="node handler.js"
|
||||
|
||||
USER 1000
|
||||
|
||||
CMD ["fwatchdog"]
|
||||
@ -1,48 +0,0 @@
|
||||
"use strict"
|
||||
let fs = require('fs');
|
||||
let sample = require("./sample.json");
|
||||
let cheerio = require('cheerio');
|
||||
let Parser = require('./parser');
|
||||
var request = require("request");
|
||||
|
||||
const getStdin = require('get-stdin');
|
||||
|
||||
getStdin().then(content => {
|
||||
let request = JSON.parse(content);
|
||||
handle(request, request.request.intent);
|
||||
});
|
||||
|
||||
function tellWithCard(speechOutput) {
|
||||
sample.response.outputSpeech.text = speechOutput
|
||||
sample.response.card.content = speechOutput
|
||||
sample.response.card.title = "Captains";
|
||||
console.log(JSON.stringify(sample));
|
||||
process.exit(0);
|
||||
}
|
||||
|
||||
function handle(request, intent) {
|
||||
createList((sorted) => {
|
||||
let speechOutput = "There are currently " + sorted.length + " Docker captains.";
|
||||
tellWithCard(speechOutput);
|
||||
});
|
||||
}
|
||||
|
||||
let createList = (next) => {
|
||||
let parser = new Parser(cheerio);
|
||||
|
||||
request.get("https://www.docker.com/community/docker-captains", (err, res, text) => {
|
||||
let captains = parser.parse(text);
|
||||
|
||||
let valid = 0;
|
||||
let sorted = captains.sort((x,y) => {
|
||||
if(x.text > y.text) {
|
||||
return 1;
|
||||
}
|
||||
else if(x.text < y.text) {
|
||||
return -1;
|
||||
}
|
||||
return 0;
|
||||
});
|
||||
next(sorted);
|
||||
});
|
||||
};
|
||||
@ -1 +0,0 @@
|
||||
docker build -t captainsintent . ; docker service rm CaptainsIntent ; docker service create --network=functions --name CaptainsIntent captainsintent
|
||||
@ -1,17 +0,0 @@
|
||||
{
|
||||
"name": "CaptainsIntent",
|
||||
"version": "1.0.0",
|
||||
"description": "",
|
||||
"main": "handler.js",
|
||||
"scripts": {
|
||||
"test": "echo \"Error: no test specified\" && exit 1"
|
||||
},
|
||||
"keywords": [],
|
||||
"author": "",
|
||||
"license": "ISC",
|
||||
"dependencies": {
|
||||
"cheerio": "^0.22.0",
|
||||
"get-stdin": "^5.0.1",
|
||||
"request": "^2.79.0"
|
||||
}
|
||||
}
|
||||
@ -1,32 +0,0 @@
|
||||
"use strict"
|
||||
|
||||
|
||||
module.exports = class Parser {
|
||||
|
||||
constructor(cheerio) {
|
||||
this.modules = {"cheerio": cheerio };
|
||||
}
|
||||
|
||||
sanitize(handle) {
|
||||
let text = handle.toLowerCase();
|
||||
if(text[0]== "@") {
|
||||
text = text.substring(1);
|
||||
}
|
||||
if(handle.indexOf("twitter.com") > -1) {
|
||||
text = text.substring(text.lastIndexOf("\/")+1)
|
||||
}
|
||||
return {text: text, valid: text.indexOf("http") == -1};
|
||||
}
|
||||
|
||||
parse(text) {
|
||||
let $ = this.modules.cheerio.load(text);
|
||||
|
||||
let people = $("#captians .twitter_link a");
|
||||
let handles = [];
|
||||
people.each((i, person) => {
|
||||
let handle = person.attribs.href;
|
||||
handles.push(this.sanitize(handle));
|
||||
});
|
||||
return handles;
|
||||
}
|
||||
};
|
||||
@ -1,24 +0,0 @@
|
||||
{
|
||||
"session": {
|
||||
"sessionId": "SessionId.8b812aa4-765a-47b6-9949-b203e63c5480",
|
||||
"application": {
|
||||
"applicationId": "amzn1.ask.skill.72fb1025-aacc-4d05-a582-21344940c023"
|
||||
},
|
||||
"attributes": {},
|
||||
"user": {
|
||||
"userId": "amzn1.ask.account.AETXYOXCBUOCTUZE7WA2ZPZNDUMJRRZQNJ2H6NLQDVTMYXBX7JG2RA7C6PFLIM4PXVD7LIDGERLI6AJVK34KNWELGEOM33GRULMDO6XJRR77HALOUJR2YQS34UG27YCPOUGANQJDT4HMRFOWN4Z5E4VVTQ6Z5FIM6TYWFHQ2ZU6HQ47TBUMNGTQFTBIONEGELUCIEUXISRSEKOI"
|
||||
},
|
||||
"new": true
|
||||
},
|
||||
"request": {
|
||||
"type": "IntentRequest",
|
||||
"requestId": "EdwRequestId.cabcff07-8aaa-4fe6-aca0-94440051fc89",
|
||||
"locale": "en-GB",
|
||||
"timestamp": "2016-12-30T19:57:45Z",
|
||||
"intent": {
|
||||
"name": "CaptainsIntent",
|
||||
"slots": {}
|
||||
}
|
||||
},
|
||||
"version": "1.0"
|
||||
}
|
||||
@ -1,2 +0,0 @@
|
||||
#!/bin/sh
|
||||
cat request.json | node handler.js -
|
||||
@ -1,16 +0,0 @@
|
||||
{
|
||||
"version": "1.0",
|
||||
"response": {
|
||||
"outputSpeech": {
|
||||
"type": "PlainText",
|
||||
"text": "There's currently 6 people in space"
|
||||
},
|
||||
"card": {
|
||||
"content": "There's currently 6 people in space",
|
||||
"title": "People in space",
|
||||
"type": "Simple"
|
||||
},
|
||||
"shouldEndSession": true
|
||||
},
|
||||
"sessionAttributes": {}
|
||||
}
|
||||
@ -1,20 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM alpine:3.16.0 as ship
|
||||
RUN apk --update add nodejs npm
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
WORKDIR /application/
|
||||
|
||||
COPY package.json .
|
||||
RUN npm i
|
||||
COPY handler.js .
|
||||
COPY sendColor.js .
|
||||
COPY sample_response.json .
|
||||
|
||||
USER 1000
|
||||
|
||||
ENV fprocess="node handler.js"
|
||||
CMD ["fwatchdog"]
|
||||
@ -1,29 +0,0 @@
|
||||
{
|
||||
"session": {
|
||||
"sessionId": "SessionId.3f589830-c369-45a3-9c8d-7f5271777dd8",
|
||||
"application": {
|
||||
"applicationId": "amzn1.ask.skill.b32fb0db-f0f0-4e64-b862-48e506f4ea68"
|
||||
},
|
||||
"attributes": {},
|
||||
"user": {
|
||||
"userId": "amzn1.ask.account.AEUHSFGVXWOYRSM2A7SVAK47L3I44TVOG6DBCTY2ACYSCUYQ65MWDZLUBZHLDD3XEMCYRLS4VSA54PQ7QBQW6FZLRJSMP5BOZE2B52YURUOSNOWORL44QGYDRXR3H7A7Y33OP3XKMUSJXIAFH7T2ZA6EQBLYRD34BPLTJXE3PDZE3V4YNFYUECXQNNH4TRG3ZBOYH2BF4BTKIIQ"
|
||||
},
|
||||
"new": true
|
||||
},
|
||||
"request": {
|
||||
"type": "IntentRequest",
|
||||
"requestId": "EdwRequestId.9ddf1ea0-c582-4dd0-8547-359f71639c1d",
|
||||
"locale": "en-GB",
|
||||
"timestamp": "2017-01-28T11:02:59Z",
|
||||
"intent": {
|
||||
"name": "ChangeColorIntent",
|
||||
"slots": {
|
||||
"LedColor": {
|
||||
"name": "LedColor",
|
||||
"value": "blue"
|
||||
}
|
||||
}
|
||||
}
|
||||
},
|
||||
"version": "1.0"
|
||||
}
|
||||
@ -1,29 +0,0 @@
|
||||
{
|
||||
"session": {
|
||||
"sessionId": "SessionId.ce487e6e-9975-4c95-b305-2a0b354f3ee0",
|
||||
"application": {
|
||||
"applicationId": "amzn1.ask.skill.dc0c07b4-e18d-4f6f-a571-90cd1aca3bc6"
|
||||
},
|
||||
"attributes": {},
|
||||
"user": {
|
||||
"userId": "amzn1.ask.account.AEFGBTDIPL5K3HYKXGNAXDHANW2MPMFRRM5QX7FCMUEOJYCGNIVUTVR7IUUHZ2VFPIDNOPIUBWZLGYSSLOBLZ6FR5FRUJMP3OAZKUI3ZZ4ADLR7M4ROICY5H5RFASQLTV5IUNIOTA7OP6N2ZNCXXZDXS7BVGPB6GKIWZAJRHOGUYSBHX2JMSLNPQ6V6HMFKGKZLAWLHKGYEUDBI"
|
||||
},
|
||||
"new": true
|
||||
},
|
||||
"request": {
|
||||
"type": "IntentRequest",
|
||||
"requestId": "EdwRequestId.ee57cb67-a465-4d93-9ea8-29229f2634bc",
|
||||
"locale": "en-GB",
|
||||
"timestamp": "2017-01-28T11:32:04Z",
|
||||
"intent": {
|
||||
"name": "ChangeColorIntent",
|
||||
"slots": {
|
||||
"LedColor": {
|
||||
"name": "LedColor",
|
||||
"value": "green"
|
||||
}
|
||||
}
|
||||
}
|
||||
},
|
||||
"version": "1.0"
|
||||
}
|
||||
@ -1,54 +0,0 @@
|
||||
"use strict"
|
||||
let fs = require('fs');
|
||||
let sample = require("./sample_response.json");
|
||||
let SendColor = require('./sendColor');
|
||||
let sendColor = new SendColor("alexellis.io/officelights")
|
||||
|
||||
const getStdin = require('get-stdin');
|
||||
|
||||
getStdin().then(content => {
|
||||
let request = JSON.parse(content);
|
||||
handle(request, request.request.intent);
|
||||
});
|
||||
|
||||
function tellWithCard(speechOutput, request) {
|
||||
sample.response.session = request.session;
|
||||
sample.response.outputSpeech.text = speechOutput;
|
||||
sample.response.card.content = speechOutput;
|
||||
sample.response.card.title = "Office Lights";
|
||||
|
||||
console.log(JSON.stringify(sample));
|
||||
process.exit(0);
|
||||
}
|
||||
|
||||
function handle(request, intent) {
|
||||
if(intent.name == "TurnOffIntent") {
|
||||
let req = {r:0,g:0,b:0};
|
||||
var speechOutput = "Lights off.";
|
||||
sendColor.sendColor(req, () => {
|
||||
return tellWithCard(speechOutput, request);
|
||||
});
|
||||
} else {
|
||||
let colorRequested = intent.slots.LedColor.value;
|
||||
let req = {r:0,g:0,b:0};
|
||||
if(colorRequested == "red") {
|
||||
req.r = 255;
|
||||
} else if(colorRequested== "blue") {
|
||||
req.b = 255;
|
||||
} else if (colorRequested == "green") {
|
||||
req.g = 255;
|
||||
} else if (colorRequested == "white") {
|
||||
req.r = 255;
|
||||
req.g = 103;
|
||||
req.b = 23;
|
||||
} else {
|
||||
let msg = "I heard "+colorRequested+ " but can only show: red, green, blue and white.";
|
||||
return tellWithCard(msg, request);
|
||||
}
|
||||
|
||||
sendColor.sendColor(req, () => {
|
||||
var speechOutput = "OK, " + colorRequested + ".";
|
||||
return tellWithCard(speechOutput, request);
|
||||
});
|
||||
}
|
||||
}
|
||||
@ -1,29 +0,0 @@
|
||||
{
|
||||
"session": {
|
||||
"sessionId": "SessionId.3f589830-c369-45a3-9c8d-7f5271777dd8",
|
||||
"application": {
|
||||
"applicationId": "amzn1.ask.skill.b32fb0db-f0f0-4e64-b862-48e506f4ea68"
|
||||
},
|
||||
"attributes": {},
|
||||
"user": {
|
||||
"userId": "amzn1.ask.account.AEUHSFGVXWOYRSM2A7SVAK47L3I44TVOG6DBCTY2ACYSCUYQ65MWDZLUBZHLDD3XEMCYRLS4VSA54PQ7QBQW6FZLRJSMP5BOZE2B52YURUOSNOWORL44QGYDRXR3H7A7Y33OP3XKMUSJXIAFH7T2ZA6EQBLYRD34BPLTJXE3PDZE3V4YNFYUECXQNNH4TRG3ZBOYH2BF4BTKIIQ"
|
||||
},
|
||||
"new": true
|
||||
},
|
||||
"request": {
|
||||
"type": "IntentRequest",
|
||||
"requestId": "EdwRequestId.9ddf1ea0-c582-4dd0-8547-359f71639c1d",
|
||||
"locale": "en-GB",
|
||||
"timestamp": "2017-01-28T11:02:59Z",
|
||||
"intent": {
|
||||
"name": "TurnOffIntent",
|
||||
"slots": {
|
||||
"LedColor": {
|
||||
"name": "LedColor",
|
||||
"value": "red"
|
||||
}
|
||||
}
|
||||
}
|
||||
},
|
||||
"version": "1.0"
|
||||
}
|
||||
@ -1 +0,0 @@
|
||||
docker build -t changecolorintent . ; docker service rm ChangeColorIntent ; docker service create --network=functions --name ChangeColorIntent changecolorintent
|
||||
@ -1,16 +0,0 @@
|
||||
{
|
||||
"name": "src",
|
||||
"version": "1.0.0",
|
||||
"description": "",
|
||||
"main": "index.js",
|
||||
"scripts": {
|
||||
"test": "echo \"Error: no test specified\" && exit 1"
|
||||
},
|
||||
"keywords": [],
|
||||
"author": "",
|
||||
"license": "ISC",
|
||||
"dependencies": {
|
||||
"get-stdin": "^5.0.1",
|
||||
"mqtt": "^2.0.1"
|
||||
}
|
||||
}
|
||||
@ -1,29 +0,0 @@
|
||||
{
|
||||
"session": {
|
||||
"sessionId": "SessionId.3f589830-c369-45a3-9c8d-7f5271777dd8",
|
||||
"application": {
|
||||
"applicationId": "amzn1.ask.skill.b32fb0db-f0f0-4e64-b862-48e506f4ea68"
|
||||
},
|
||||
"attributes": {},
|
||||
"user": {
|
||||
"userId": "amzn1.ask.account.AEUHSFGVXWOYRSM2A7SVAK47L3I44TVOG6DBCTY2ACYSCUYQ65MWDZLUBZHLDD3XEMCYRLS4VSA54PQ7QBQW6FZLRJSMP5BOZE2B52YURUOSNOWORL44QGYDRXR3H7A7Y33OP3XKMUSJXIAFH7T2ZA6EQBLYRD34BPLTJXE3PDZE3V4YNFYUECXQNNH4TRG3ZBOYH2BF4BTKIIQ"
|
||||
},
|
||||
"new": true
|
||||
},
|
||||
"request": {
|
||||
"type": "IntentRequest",
|
||||
"requestId": "EdwRequestId.9ddf1ea0-c582-4dd0-8547-359f71639c1d",
|
||||
"locale": "en-GB",
|
||||
"timestamp": "2017-01-28T11:02:59Z",
|
||||
"intent": {
|
||||
"name": "ChangeColorIntent",
|
||||
"slots": {
|
||||
"LedColor": {
|
||||
"name": "LedColor",
|
||||
"value": "red"
|
||||
}
|
||||
}
|
||||
}
|
||||
},
|
||||
"version": "1.0"
|
||||
}
|
||||
@ -1,29 +0,0 @@
|
||||
{
|
||||
"session": {
|
||||
"sessionId": "SessionId.3f589830-c369-45a3-9c8d-7f5271777dd8",
|
||||
"application": {
|
||||
"applicationId": "amzn1.ask.skill.b32fb0db-f0f0-4e64-b862-48e506f4ea68"
|
||||
},
|
||||
"attributes": {},
|
||||
"user": {
|
||||
"userId": "amzn1.ask.account.AEUHSFGVXWOYRSM2A7SVAK47L3I44TVOG6DBCTY2ACYSCUYQ65MWDZLUBZHLDD3XEMCYRLS4VSA54PQ7QBQW6FZLRJSMP5BOZE2B52YURUOSNOWORL44QGYDRXR3H7A7Y33OP3XKMUSJXIAFH7T2ZA6EQBLYRD34BPLTJXE3PDZE3V4YNFYUECXQNNH4TRG3ZBOYH2BF4BTKIIQ"
|
||||
},
|
||||
"new": true
|
||||
},
|
||||
"request": {
|
||||
"type": "IntentRequest",
|
||||
"requestId": "EdwRequestId.9ddf1ea0-c582-4dd0-8547-359f71639c1d",
|
||||
"locale": "en-GB",
|
||||
"timestamp": "2017-01-28T11:02:59Z",
|
||||
"intent": {
|
||||
"name": "ChangeColorIntent",
|
||||
"slots": {
|
||||
"LedColor": {
|
||||
"name": "LedColor",
|
||||
"value": "blue"
|
||||
}
|
||||
}
|
||||
}
|
||||
},
|
||||
"version": "1.0"
|
||||
}
|
||||
@ -1,16 +0,0 @@
|
||||
{
|
||||
"version": "1.0",
|
||||
"response": {
|
||||
"outputSpeech": {
|
||||
"type": "PlainText",
|
||||
"text": "OK, red."
|
||||
},
|
||||
"card": {
|
||||
"content": "OK, red.",
|
||||
"title": "Office Lights",
|
||||
"type": "Simple"
|
||||
},
|
||||
"shouldEndSession": true
|
||||
},
|
||||
"sessionAttributes": {}
|
||||
}
|
||||
@ -1,40 +0,0 @@
|
||||
"use strict"
|
||||
|
||||
var mqtt = require('mqtt');
|
||||
|
||||
class Send {
|
||||
constructor(topic) {
|
||||
this.topic = topic;
|
||||
}
|
||||
|
||||
sendIntensity(req, done) {
|
||||
var ops = { port: 1883, host: "iot.eclipse.org" };
|
||||
|
||||
var client = mqtt.connect(ops);
|
||||
|
||||
client.on('connect', () => {
|
||||
|
||||
let payload = req;
|
||||
let cb = () => {
|
||||
done();
|
||||
};
|
||||
client.publish(this.topic, JSON.stringify(payload), {qos: 1}, cb);
|
||||
});
|
||||
}
|
||||
|
||||
sendColor(req, done) {
|
||||
var ops = { port: 1883, host: "iot.eclipse.org" };
|
||||
|
||||
var client = mqtt.connect(ops);
|
||||
let cb = () => {
|
||||
done();
|
||||
};
|
||||
client.on('connect', () => {
|
||||
|
||||
let payload = req;
|
||||
client.publish(this.topic, JSON.stringify(payload), {qos: 1}, cb);
|
||||
});
|
||||
}
|
||||
}
|
||||
|
||||
module.exports = Send;
|
||||
1
sample-functions/DockerHubStats/.gitignore
vendored
1
sample-functions/DockerHubStats/.gitignore
vendored
@ -1 +0,0 @@
|
||||
DockerHubStats
|
||||
@ -1,27 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM golang:1.13-alpine as builder
|
||||
ENV CGO_ENABLED=0
|
||||
|
||||
MAINTAINER alex@openfaas.com
|
||||
ENTRYPOINT []
|
||||
|
||||
WORKDIR /go/src/github.com/openfaas/faas/sample-functions/DockerHubStats
|
||||
COPY . /go/src/github.com/openfaas/faas/sample-functions/DockerHubStats
|
||||
RUN set -ex && apk add make && make install
|
||||
|
||||
FROM alpine:3.16.0 as ship
|
||||
|
||||
# Needed to reach the hub
|
||||
RUN apk --no-cache add ca-certificates
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
COPY --from=builder /go/bin/DockerHubStats /usr/bin/DockerHubStats
|
||||
ENV fprocess "/usr/bin/DockerHubStats"
|
||||
|
||||
RUN addgroup -g 1000 -S app && adduser -u 1000 -S app -G app
|
||||
USER 1000
|
||||
|
||||
HEALTHCHECK --interval=5s CMD [ -e /tmp/.lock ] || exit 1
|
||||
CMD ["/usr/bin/fwatchdog"]
|
||||
@ -1,25 +0,0 @@
|
||||
FROM golang:1.9.7-alpine as builder
|
||||
|
||||
MAINTAINER alex@openfaas.com
|
||||
ENTRYPOINT []
|
||||
|
||||
RUN apk --no-cache add make curl \
|
||||
&& curl -sL https://github.com/openfaas/faas/releases/download/0.13.0/fwatchdog-armhf > /usr/bin/fwatchdog \
|
||||
&& chmod +x /usr/bin/fwatchdog
|
||||
|
||||
WORKDIR /go/src/github.com/openfaas/faas/sample-functions/DockerHubStats
|
||||
|
||||
COPY . /go/src/github.com/openfaas/faas/sample-functions/DockerHubStats
|
||||
|
||||
RUN make install
|
||||
|
||||
FROM alpine:3.16.0 as ship
|
||||
|
||||
# Needed to reach the hub
|
||||
RUN apk --no-cache add ca-certificates
|
||||
|
||||
COPY --from=builder /usr/bin/fwatchdog /usr/bin/fwatchdog
|
||||
COPY --from=builder /go/bin/DockerHubStats /usr/bin/DockerHubStats
|
||||
ENV fprocess "/usr/bin/DockerHubStats"
|
||||
|
||||
CMD ["/usr/bin/fwatchdog"]
|
||||
@ -1,5 +0,0 @@
|
||||
|
||||
.PHONY: install
|
||||
|
||||
install:
|
||||
@go install .
|
||||
@ -1,81 +0,0 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"encoding/json"
|
||||
"fmt"
|
||||
"io/ioutil"
|
||||
"log"
|
||||
"net/http"
|
||||
"os"
|
||||
"strings"
|
||||
)
|
||||
|
||||
type dockerHubOrgStatsType struct {
|
||||
Count int `json:"count"`
|
||||
}
|
||||
|
||||
type dockerHubRepoStatsType struct {
|
||||
PullCount int `json:"pull_count"`
|
||||
}
|
||||
|
||||
func sanitizeInput(input string) string {
|
||||
parts := strings.Split(input, "\n")
|
||||
return strings.Trim(parts[0], " ")
|
||||
}
|
||||
|
||||
func requestStats(repo string) []byte {
|
||||
client := http.Client{}
|
||||
res, err := client.Get("https://hub.docker.com/v2/repositories/" + repo)
|
||||
if err != nil {
|
||||
log.Fatalln("Unable to reach Docker Hub server.")
|
||||
}
|
||||
|
||||
body, err := ioutil.ReadAll(res.Body)
|
||||
if err != nil {
|
||||
log.Fatalln("Unable to parse response from server.")
|
||||
}
|
||||
|
||||
return body
|
||||
}
|
||||
|
||||
func parseOrgStats(response []byte) (dockerHubOrgStatsType, error) {
|
||||
dockerHubOrgStats := dockerHubOrgStatsType{}
|
||||
err := json.Unmarshal(response, &dockerHubOrgStats)
|
||||
return dockerHubOrgStats, err
|
||||
}
|
||||
|
||||
func parseRepoStats(response []byte) (dockerHubRepoStatsType, error) {
|
||||
dockerHubRepoStats := dockerHubRepoStatsType{}
|
||||
err := json.Unmarshal(response, &dockerHubRepoStats)
|
||||
return dockerHubRepoStats, err
|
||||
}
|
||||
|
||||
func main() {
|
||||
input, err := ioutil.ReadAll(os.Stdin)
|
||||
if err != nil {
|
||||
log.Fatal("Unable to read standard input:", err)
|
||||
}
|
||||
request := string(input)
|
||||
if len(input) == 0 {
|
||||
log.Fatalln("A username/organisation or repository is required.")
|
||||
}
|
||||
|
||||
request = sanitizeInput(request)
|
||||
response := requestStats(request)
|
||||
|
||||
if strings.Contains(request, "/") {
|
||||
dockerHubRepoStats, err := parseRepoStats(response)
|
||||
if err != nil {
|
||||
log.Fatalln("Unable to parse response from Docker Hub for repository")
|
||||
} else {
|
||||
fmt.Printf("Repo: %s has been pulled %d times from the Docker Hub", request, dockerHubRepoStats.PullCount)
|
||||
}
|
||||
} else {
|
||||
dockerHubOrgStats, err := parseOrgStats(response)
|
||||
if err != nil {
|
||||
log.Fatalln("Unable to parse response from Docker Hub for user/organisation")
|
||||
} else {
|
||||
fmt.Printf("The organisation or user %s has %d repositories on the Docker hub.\n", request, dockerHubOrgStats.Count)
|
||||
}
|
||||
}
|
||||
}
|
||||
@ -1,16 +0,0 @@
|
||||
FROM functions/alpine:latest
|
||||
|
||||
USER root
|
||||
|
||||
RUN apk --update add nodejs npm
|
||||
|
||||
COPY package.json .
|
||||
COPY handler.js .
|
||||
COPY sample.json .
|
||||
|
||||
RUN npm i
|
||||
|
||||
USER 1000
|
||||
|
||||
ENV fprocess="node handler.js"
|
||||
CMD ["fwatchdog"]
|
||||
@ -1,26 +0,0 @@
|
||||
"use strict"
|
||||
let fs = require('fs');
|
||||
let sample = require("./sample.json");
|
||||
let getStdin = require("get-stdin");
|
||||
|
||||
getStdin().then(content => {
|
||||
let request = JSON.parse(content);
|
||||
handle(request, request.request.intent);
|
||||
});
|
||||
|
||||
function tellWithCard(speechOutput) {
|
||||
sample.response.outputSpeech.text = speechOutput
|
||||
sample.response.card.content = speechOutput
|
||||
sample.response.card.title = "Hostname";
|
||||
console.log(JSON.stringify(sample));
|
||||
process.exit(0);
|
||||
}
|
||||
|
||||
function handle(request, intent) {
|
||||
fs.readFile("/etc/hostname", "utf8", (err, data) => {
|
||||
if(err) {
|
||||
return console.log(err);
|
||||
}
|
||||
tellWithCard("Your hostname is " + data);
|
||||
});
|
||||
};
|
||||
@ -1 +0,0 @@
|
||||
docker build -t hostnameintent . ; docker service rm HostnameIntent ; docker service create --network=functions --name HostnameIntent hostnameintent
|
||||
@ -1,15 +0,0 @@
|
||||
{
|
||||
"name": "HostnameIntent",
|
||||
"version": "1.0.0",
|
||||
"description": "",
|
||||
"main": "handler.js",
|
||||
"scripts": {
|
||||
"test": "echo \"Error: no test specified\" && exit 1"
|
||||
},
|
||||
"keywords": [],
|
||||
"author": "",
|
||||
"license": "ISC",
|
||||
"dependencies": {
|
||||
"get-stdin": "^5.0.1"
|
||||
}
|
||||
}
|
||||
@ -1,16 +0,0 @@
|
||||
{
|
||||
"version": "1.0",
|
||||
"response": {
|
||||
"outputSpeech": {
|
||||
"type": "PlainText",
|
||||
"text": "There's currently 6 people in space"
|
||||
},
|
||||
"card": {
|
||||
"content": "There's currently 6 people in space",
|
||||
"title": "People in space",
|
||||
"type": "Simple"
|
||||
},
|
||||
"shouldEndSession": true
|
||||
},
|
||||
"sessionAttributes": {}
|
||||
}
|
||||
2
sample-functions/MarkdownRender/.gitignore
vendored
2
sample-functions/MarkdownRender/.gitignore
vendored
@ -1,2 +0,0 @@
|
||||
app
|
||||
MarkdownRender
|
||||
@ -1,27 +0,0 @@
|
||||
FROM ghcr.io/openfaas/classic-watchdog:0.2.0 as watchdog
|
||||
|
||||
FROM golang:1.13-alpine as builder
|
||||
ENV CGO_ENABLED=0
|
||||
|
||||
MAINTAINER alex@openfaas.com
|
||||
ENTRYPOINT []
|
||||
|
||||
WORKDIR /go/src/github.com/openfaas/faas/sample-functions/MarkdownRender
|
||||
|
||||
COPY handler.go .
|
||||
COPY vendor vendor
|
||||
|
||||
RUN go install
|
||||
|
||||
FROM alpine:3.16.0 as ship
|
||||
|
||||
COPY --from=watchdog /fwatchdog /usr/bin/fwatchdog
|
||||
RUN chmod +x /usr/bin/fwatchdog
|
||||
|
||||
COPY --from=builder /go/bin/MarkdownRender /usr/bin/MarkdownRender
|
||||
ENV fprocess "/usr/bin/MarkdownRender"
|
||||
|
||||
RUN addgroup -g 1000 -S app && adduser -u 1000 -S app -G app
|
||||
USER 1000
|
||||
|
||||
CMD ["/usr/bin/fwatchdog"]
|
||||
33
sample-functions/MarkdownRender/Gopkg.lock
generated
33
sample-functions/MarkdownRender/Gopkg.lock
generated
@ -1,33 +0,0 @@
|
||||
# This file is autogenerated, do not edit; changes may be undone by the next 'dep ensure'.
|
||||
|
||||
|
||||
[[projects]]
|
||||
branch = "master"
|
||||
name = "github.com/microcosm-cc/bluemonday"
|
||||
packages = ["."]
|
||||
revision = "68fecaef60268522d2ac3f0123cec9d3bcab7b6e"
|
||||
|
||||
[[projects]]
|
||||
name = "github.com/russross/blackfriday"
|
||||
packages = ["."]
|
||||
revision = "cadec560ec52d93835bf2f15bd794700d3a2473b"
|
||||
version = "v2.0.0"
|
||||
|
||||
[[projects]]
|
||||
branch = "master"
|
||||
name = "github.com/shurcooL/sanitized_anchor_name"
|
||||
packages = ["."]
|
||||
revision = "86672fcb3f950f35f2e675df2240550f2a50762f"
|
||||
|
||||
[[projects]]
|
||||
branch = "master"
|
||||
name = "golang.org/x/net"
|
||||
packages = ["html","html/atom"]
|
||||
revision = "a337091b0525af65de94df2eb7e98bd9962dcbe2"
|
||||
|
||||
[solve-meta]
|
||||
analyzer-name = "dep"
|
||||
analyzer-version = 1
|
||||
inputs-digest = "501ddd966c3f040b4158a459f36eeda2818e57897613b965188a4f4b15579034"
|
||||
solver-name = "gps-cdcl"
|
||||
solver-version = 1
|
||||
@ -1,30 +0,0 @@
|
||||
|
||||
# Gopkg.toml example
|
||||
#
|
||||
# Refer to https://github.com/golang/dep/blob/master/docs/Gopkg.toml.md
|
||||
# for detailed Gopkg.toml documentation.
|
||||
#
|
||||
# required = ["github.com/user/thing/cmd/thing"]
|
||||
# ignored = ["github.com/user/project/pkgX", "bitbucket.org/user/project/pkgA/pkgY"]
|
||||
#
|
||||
# [[constraint]]
|
||||
# name = "github.com/user/project"
|
||||
# version = "1.0.0"
|
||||
#
|
||||
# [[constraint]]
|
||||
# name = "github.com/user/project2"
|
||||
# branch = "dev"
|
||||
# source = "github.com/myfork/project2"
|
||||
#
|
||||
# [[override]]
|
||||
# name = "github.com/x/y"
|
||||
# version = "2.4.0"
|
||||
|
||||
|
||||
[[constraint]]
|
||||
branch = "master"
|
||||
name = "github.com/microcosm-cc/bluemonday"
|
||||
|
||||
[[constraint]]
|
||||
name = "github.com/russross/blackfriday"
|
||||
version = "2.0.0"
|
||||
@ -1,17 +0,0 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"io/ioutil"
|
||||
"os"
|
||||
|
||||
"github.com/microcosm-cc/bluemonday"
|
||||
"github.com/russross/blackfriday"
|
||||
)
|
||||
|
||||
func main() {
|
||||
input, _ := ioutil.ReadAll(os.Stdin)
|
||||
unsafe := blackfriday.Run([]byte(input), blackfriday.WithNoExtensions())
|
||||
html := bluemonday.UGCPolicy().SanitizeBytes(unsafe)
|
||||
fmt.Println(string(html))
|
||||
}
|
||||
@ -1 +0,0 @@
|
||||
repo_token: x2wlA1x0X8CK45ybWpZRCVRB4g7vtkhaw
|
||||
20
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/.travis.yml
generated
vendored
20
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/.travis.yml
generated
vendored
@ -1,20 +0,0 @@
|
||||
language: go
|
||||
go:
|
||||
- 1.1
|
||||
- 1.2
|
||||
- 1.3
|
||||
- 1.4
|
||||
- 1.5
|
||||
- 1.6
|
||||
- 1.7
|
||||
- 1.8
|
||||
- 1.9
|
||||
- tip
|
||||
matrix:
|
||||
allow_failures:
|
||||
- go: tip
|
||||
fast_finish: true
|
||||
install:
|
||||
- go get golang.org/x/net/html
|
||||
script:
|
||||
- go test -v ./...
|
||||
@ -1,51 +0,0 @@
|
||||
# Contributing to bluemonday
|
||||
|
||||
Third-party patches are essential for keeping bluemonday secure and offering the features developers want. However there are a few guidelines that we need contributors to follow so that we can maintain the quality of work that developers who use bluemonday expect.
|
||||
|
||||
## Getting Started
|
||||
|
||||
* Make sure you have a [Github account](https://github.com/signup/free)
|
||||
|
||||
## Guidelines
|
||||
|
||||
1. Do not vendor dependencies. As a security package, were we to vendor dependencies the projects that then vendor bluemonday may not receive the latest security updates to the dependencies. By not vendoring dependencies the project that implements bluemonday will vendor the latest version of any dependent packages. Vendoring is a project problem, not a package problem. bluemonday will be tested against the latest version of dependencies periodically and during any PR/merge.
|
||||
|
||||
## Submitting an Issue
|
||||
|
||||
* Submit a ticket for your issue, assuming one does not already exist
|
||||
* Clearly describe the issue including the steps to reproduce (with sample input and output) if it is a bug
|
||||
|
||||
If you are reporting a security flaw, you may expect that we will provide the code to fix it for you. Otherwise you may want to submit a pull request to ensure the resolution is applied sooner rather than later:
|
||||
|
||||
* Fork the repository on Github
|
||||
* Issue a pull request containing code to resolve the issue
|
||||
|
||||
## Submitting a Pull Request
|
||||
|
||||
* Submit a ticket for your issue, assuming one does not already exist
|
||||
* Describe the reason for the pull request and if applicable show some example inputs and outputs to demonstrate what the patch does
|
||||
* Fork the repository on Github
|
||||
* Before submitting the pull request you should
|
||||
1. Include tests for your patch, 1 test should encapsulate the entire patch and should refer to the Github issue
|
||||
1. If you have added new exposed/public functionality, you should ensure it is documented appropriately
|
||||
1. If you have added new exposed/public functionality, you should consider demonstrating how to use it within one of the helpers or shipped policies if appropriate or within a test if modifying a helper or policy is not appropriate
|
||||
1. Run all of the tests `go test -v ./...` or `make test` and ensure all tests pass
|
||||
1. Run gofmt `gofmt -w ./$*` or `make fmt`
|
||||
1. Run vet `go tool vet *.go` or `make vet` and resolve any issues
|
||||
1. Install golint using `go get -u github.com/golang/lint/golint` and run vet `golint *.go` or `make lint` and resolve every warning
|
||||
* When submitting the pull request you should
|
||||
1. Note the issue(s) it resolves, i.e. `Closes #6` in the pull request comment to close issue #6 when the pull request is accepted
|
||||
|
||||
Once you have submitted a pull request, we *may* merge it without changes. If we have any comments or feedback, or need you to make changes to your pull request we will update the Github pull request or the associated issue. We expect responses from you within two weeks, and we may close the pull request is there is no activity.
|
||||
|
||||
### Contributor Licence Agreement
|
||||
|
||||
We haven't gone for the formal "Sign a Contributor Licence Agreement" thing that projects like [puppet](https://cla.puppetlabs.com/), [Mojito](https://developer.yahoo.com/cocktails/mojito/cla/) and companies like [Google](http://code.google.com/legal/individual-cla-v1.0.html) are using.
|
||||
|
||||
But we do need to know that we can accept and merge your contributions, so for now the act of contributing a pull request should be considered equivalent to agreeing to a contributor licence agreement, specifically:
|
||||
|
||||
You accept that the act of submitting code to the bluemonday project is to grant a copyright licence to the project that is perpetual, worldwide, non-exclusive, no-charge, royalty free and irrevocable.
|
||||
|
||||
You accept that all who comply with the licence of the project (BSD 3-clause) are permitted to use your contributions to the project.
|
||||
|
||||
You accept, and by submitting code do declare, that you have the legal right to grant such a licence to the project and that each of the contributions is your own original creation.
|
||||
6
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/CREDITS.md
generated
vendored
6
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/CREDITS.md
generated
vendored
@ -1,6 +0,0 @@
|
||||
|
||||
1. John Graham-Cumming http://jgc.org/
|
||||
1. Mike Samuel mikesamuel@gmail.com
|
||||
1. Dmitri Shuralyov shurcooL@gmail.com
|
||||
1. https://github.com/opennota
|
||||
1. https://github.com/Gufran
|
||||
28
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/LICENSE.md
generated
vendored
28
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/LICENSE.md
generated
vendored
@ -1,28 +0,0 @@
|
||||
Copyright (c) 2014, David Kitchen <david@buro9.com>
|
||||
|
||||
All rights reserved.
|
||||
|
||||
Redistribution and use in source and binary forms, with or without
|
||||
modification, are permitted provided that the following conditions are met:
|
||||
|
||||
* Redistributions of source code must retain the above copyright notice, this
|
||||
list of conditions and the following disclaimer.
|
||||
|
||||
* Redistributions in binary form must reproduce the above copyright notice,
|
||||
this list of conditions and the following disclaimer in the documentation
|
||||
and/or other materials provided with the distribution.
|
||||
|
||||
* Neither the name of the organisation (Microcosm) nor the names of its
|
||||
contributors may be used to endorse or promote products derived from
|
||||
this software without specific prior written permission.
|
||||
|
||||
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
|
||||
AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
|
||||
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
|
||||
DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
|
||||
FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
|
||||
DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
|
||||
SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
|
||||
CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
|
||||
OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
|
||||
OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
42
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/Makefile
generated
vendored
42
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/Makefile
generated
vendored
@ -1,42 +0,0 @@
|
||||
# Targets:
|
||||
#
|
||||
# all: Builds the code locally after testing
|
||||
#
|
||||
# fmt: Formats the source files
|
||||
# build: Builds the code locally
|
||||
# vet: Vets the code
|
||||
# lint: Runs lint over the code (you do not need to fix everything)
|
||||
# test: Runs the tests
|
||||
# cover: Gives you the URL to a nice test coverage report
|
||||
#
|
||||
# install: Builds, tests and installs the code locally
|
||||
|
||||
.PHONY: all fmt build vet lint test cover install
|
||||
|
||||
# The first target is always the default action if `make` is called without
|
||||
# args we build and install into $GOPATH so that it can just be run
|
||||
|
||||
all: fmt vet test install
|
||||
|
||||
fmt:
|
||||
@gofmt -s -w ./$*
|
||||
|
||||
build:
|
||||
@go build
|
||||
|
||||
vet:
|
||||
@go vet *.go
|
||||
|
||||
lint:
|
||||
@golint *.go
|
||||
|
||||
test:
|
||||
@go test -v ./...
|
||||
|
||||
cover: COVERAGE_FILE := coverage.out
|
||||
cover:
|
||||
@go test -coverprofile=$(COVERAGE_FILE) && \
|
||||
cover -html=$(COVERAGE_FILE) && rm $(COVERAGE_FILE)
|
||||
|
||||
install:
|
||||
@go install ./...
|
||||
346
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/README.md
generated
vendored
346
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/README.md
generated
vendored
@ -1,346 +0,0 @@
|
||||
# bluemonday [](https://travis-ci.org/microcosm-cc/bluemonday) [](https://godoc.org/github.com/microcosm-cc/bluemonday) [](https://sourcegraph.com/github.com/microcosm-cc/bluemonday?badge)
|
||||
|
||||
bluemonday is a HTML sanitizer implemented in Go. It is fast and highly configurable.
|
||||
|
||||
bluemonday takes untrusted user generated content as an input, and will return HTML that has been sanitised against a whitelist of approved HTML elements and attributes so that you can safely include the content in your web page.
|
||||
|
||||
If you accept user generated content, and your server uses Go, you **need** bluemonday.
|
||||
|
||||
The default policy for user generated content (`bluemonday.UGCPolicy().Sanitize()`) turns this:
|
||||
```html
|
||||
Hello <STYLE>.XSS{background-image:url("javascript:alert('XSS')");}</STYLE><A CLASS=XSS></A>World
|
||||
```
|
||||
|
||||
Into a harmless:
|
||||
```html
|
||||
Hello World
|
||||
```
|
||||
|
||||
And it turns this:
|
||||
```html
|
||||
<a href="javascript:alert('XSS1')" onmouseover="alert('XSS2')">XSS<a>
|
||||
```
|
||||
|
||||
Into this:
|
||||
```html
|
||||
XSS
|
||||
```
|
||||
|
||||
Whilst still allowing this:
|
||||
```html
|
||||
<a href="http://www.google.com/">
|
||||
<img src="https://ssl.gstatic.com/accounts/ui/logo_2x.png"/>
|
||||
</a>
|
||||
```
|
||||
|
||||
To pass through mostly unaltered (it gained a rel="nofollow" which is a good thing for user generated content):
|
||||
```html
|
||||
<a href="http://www.google.com/" rel="nofollow">
|
||||
<img src="https://ssl.gstatic.com/accounts/ui/logo_2x.png"/>
|
||||
</a>
|
||||
```
|
||||
|
||||
It protects sites from [XSS](http://en.wikipedia.org/wiki/Cross-site_scripting) attacks. There are many [vectors for an XSS attack](https://www.owasp.org/index.php/XSS_Filter_Evasion_Cheat_Sheet) and the best way to mitigate the risk is to sanitize user input against a known safe list of HTML elements and attributes.
|
||||
|
||||
You should **always** run bluemonday **after** any other processing.
|
||||
|
||||
If you use [blackfriday](https://github.com/russross/blackfriday) or [Pandoc](http://johnmacfarlane.net/pandoc/) then bluemonday should be run after these steps. This ensures that no insecure HTML is introduced later in your process.
|
||||
|
||||
bluemonday is heavily inspired by both the [OWASP Java HTML Sanitizer](https://code.google.com/p/owasp-java-html-sanitizer/) and the [HTML Purifier](http://htmlpurifier.org/).
|
||||
|
||||
## Technical Summary
|
||||
|
||||
Whitelist based, you need to either build a policy describing the HTML elements and attributes to permit (and the `regexp` patterns of attributes), or use one of the supplied policies representing good defaults.
|
||||
|
||||
The policy containing the whitelist is applied using a fast non-validating, forward only, token-based parser implemented in the [Go net/html library](https://godoc.org/golang.org/x/net/html) by the core Go team.
|
||||
|
||||
We expect to be supplied with well-formatted HTML (closing elements for every applicable open element, nested correctly) and so we do not focus on repairing badly nested or incomplete HTML. We focus on simply ensuring that whatever elements do exist are described in the policy whitelist and that attributes and links are safe for use on your web page. [GIGO](http://en.wikipedia.org/wiki/Garbage_in,_garbage_out) does apply and if you feed it bad HTML bluemonday is not tasked with figuring out how to make it good again.
|
||||
|
||||
### Supported Go Versions
|
||||
|
||||
bluemonday is tested against Go 1.1, 1.2, 1.3, 1.4, 1.5, 1.6, 1.7, 1.8, 1.9, and tip.
|
||||
|
||||
We do not support Go 1.0 as we depend on `golang.org/x/net/html` which includes a reference to `io.ErrNoProgress` which did not exist in Go 1.0.
|
||||
|
||||
## Is it production ready?
|
||||
|
||||
*Yes*
|
||||
|
||||
We are using bluemonday in production having migrated from the widely used and heavily field tested OWASP Java HTML Sanitizer.
|
||||
|
||||
We are passing our extensive test suite (including AntiSamy tests as well as tests for any issues raised). Check for any [unresolved issues](https://github.com/microcosm-cc/bluemonday/issues?page=1&state=open) to see whether anything may be a blocker for you.
|
||||
|
||||
We invite pull requests and issues to help us ensure we are offering comprehensive protection against various attacks via user generated content.
|
||||
|
||||
## Usage
|
||||
|
||||
Install in your `${GOPATH}` using `go get -u github.com/microcosm-cc/bluemonday`
|
||||
|
||||
Then call it:
|
||||
```go
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
|
||||
"github.com/microcosm-cc/bluemonday"
|
||||
)
|
||||
|
||||
func main() {
|
||||
p := bluemonday.UGCPolicy()
|
||||
html := p.Sanitize(
|
||||
`<a onblur="alert(secret)" href="http://www.google.com">Google</a>`,
|
||||
)
|
||||
|
||||
// Output:
|
||||
// <a href="http://www.google.com" rel="nofollow">Google</a>
|
||||
fmt.Println(html)
|
||||
}
|
||||
```
|
||||
|
||||
We offer three ways to call Sanitize:
|
||||
```go
|
||||
p.Sanitize(string) string
|
||||
p.SanitizeBytes([]byte) []byte
|
||||
p.SanitizeReader(io.Reader) bytes.Buffer
|
||||
```
|
||||
|
||||
If you are obsessed about performance, `p.SanitizeReader(r).Bytes()` will return a `[]byte` without performing any unnecessary casting of the inputs or outputs. Though the difference is so negligible you should never need to care.
|
||||
|
||||
You can build your own policies:
|
||||
```go
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
|
||||
"github.com/microcosm-cc/bluemonday"
|
||||
)
|
||||
|
||||
func main() {
|
||||
p := bluemonday.NewPolicy()
|
||||
|
||||
// Require URLs to be parseable by net/url.Parse and either:
|
||||
// mailto: http:// or https://
|
||||
p.AllowStandardURLs()
|
||||
|
||||
// We only allow <p> and <a href="">
|
||||
p.AllowAttrs("href").OnElements("a")
|
||||
p.AllowElements("p")
|
||||
|
||||
html := p.Sanitize(
|
||||
`<a onblur="alert(secret)" href="http://www.google.com">Google</a>`,
|
||||
)
|
||||
|
||||
// Output:
|
||||
// <a href="http://www.google.com">Google</a>
|
||||
fmt.Println(html)
|
||||
}
|
||||
```
|
||||
|
||||
We ship two default policies:
|
||||
|
||||
1. `bluemonday.StrictPolicy()` which can be thought of as equivalent to stripping all HTML elements and their attributes as it has nothing on it's whitelist. An example usage scenario would be blog post titles where HTML tags are not expected at all and if they are then the elements *and* the content of the elements should be stripped. This is a *very* strict policy.
|
||||
2. `bluemonday.UGCPolicy()` which allows a broad selection of HTML elements and attributes that are safe for user generated content. Note that this policy does *not* whitelist iframes, object, embed, styles, script, etc. An example usage scenario would be blog post bodies where a variety of formatting is expected along with the potential for TABLEs and IMGs.
|
||||
|
||||
## Policy Building
|
||||
|
||||
The essence of building a policy is to determine which HTML elements and attributes are considered safe for your scenario. OWASP provide an [XSS prevention cheat sheet](https://www.owasp.org/index.php/XSS_(Cross_Site_Scripting)_Prevention_Cheat_Sheet) to help explain the risks, but essentially:
|
||||
|
||||
1. Avoid anything other than the standard HTML elements
|
||||
1. Avoid `script`, `style`, `iframe`, `object`, `embed`, `base` elements that allow code to be executed by the client or third party content to be included that can execute code
|
||||
1. Avoid anything other than plain HTML attributes with values matched to a regexp
|
||||
|
||||
Basically, you should be able to describe what HTML is fine for your scenario. If you do not have confidence that you can describe your policy please consider using one of the shipped policies such as `bluemonday.UGCPolicy()`.
|
||||
|
||||
To create a new policy:
|
||||
```go
|
||||
p := bluemonday.NewPolicy()
|
||||
```
|
||||
|
||||
To add elements to a policy either add just the elements:
|
||||
```go
|
||||
p.AllowElements("b", "strong")
|
||||
```
|
||||
|
||||
Or add elements as a virtue of adding an attribute:
|
||||
```go
|
||||
// Not the recommended pattern, see the recommendation on using .Matching() below
|
||||
p.AllowAttrs("nowrap").OnElements("td", "th")
|
||||
```
|
||||
|
||||
Attributes can either be added to all elements:
|
||||
```go
|
||||
p.AllowAttrs("dir").Matching(regexp.MustCompile("(?i)rtl|ltr")).Globally()
|
||||
```
|
||||
|
||||
Or attributes can be added to specific elements:
|
||||
```go
|
||||
// Not the recommended pattern, see the recommendation on using .Matching() below
|
||||
p.AllowAttrs("value").OnElements("li")
|
||||
```
|
||||
|
||||
It is **always** recommended that an attribute be made to match a pattern. XSS in HTML attributes is very easy otherwise:
|
||||
```go
|
||||
// \p{L} matches unicode letters, \p{N} matches unicode numbers
|
||||
p.AllowAttrs("title").Matching(regexp.MustCompile(`[\p{L}\p{N}\s\-_',:\[\]!\./\\\(\)&]*`)).Globally()
|
||||
```
|
||||
|
||||
You can stop at any time and call .Sanitize():
|
||||
```go
|
||||
// string htmlIn passed in from a HTTP POST
|
||||
htmlOut := p.Sanitize(htmlIn)
|
||||
```
|
||||
|
||||
And you can take any existing policy and extend it:
|
||||
```go
|
||||
p := bluemonday.UGCPolicy()
|
||||
p.AllowElements("fieldset", "select", "option")
|
||||
```
|
||||
|
||||
### Links
|
||||
|
||||
Links are difficult beasts to sanitise safely and also one of the biggest attack vectors for malicious content.
|
||||
|
||||
It is possible to do this:
|
||||
```go
|
||||
p.AllowAttrs("href").Matching(regexp.MustCompile(`(?i)mailto|https?`)).OnElements("a")
|
||||
```
|
||||
|
||||
But that will not protect you as the regular expression is insufficient in this case to have prevented a malformed value doing something unexpected.
|
||||
|
||||
We provide some additional global options for safely working with links.
|
||||
|
||||
`RequireParseableURLs` will ensure that URLs are parseable by Go's `net/url` package:
|
||||
```go
|
||||
p.RequireParseableURLs(true)
|
||||
```
|
||||
|
||||
If you have enabled parseable URLs then the following option will `AllowRelativeURLs`. By default this is disabled (bluemonday is a whitelist tool... you need to explicitly tell us to permit things) and when disabled it will prevent all local and scheme relative URLs (i.e. `href="localpage.html"`, `href="../home.html"` and even `href="//www.google.com"` are relative):
|
||||
```go
|
||||
p.AllowRelativeURLs(true)
|
||||
```
|
||||
|
||||
If you have enabled parseable URLs then you can whitelist the schemes (commonly called protocol when thinking of `http` and `https`) that are permitted. Bear in mind that allowing relative URLs in the above option will allow for a blank scheme:
|
||||
```go
|
||||
p.AllowURLSchemes("mailto", "http", "https")
|
||||
```
|
||||
|
||||
Regardless of whether you have enabled parseable URLs, you can force all URLs to have a rel="nofollow" attribute. This will be added if it does not exist, but only when the `href` is valid:
|
||||
```go
|
||||
// This applies to "a" "area" "link" elements that have a "href" attribute
|
||||
p.RequireNoFollowOnLinks(true)
|
||||
```
|
||||
|
||||
We provide a convenience method that applies all of the above, but you will still need to whitelist the linkable elements for the URL rules to be applied to:
|
||||
```go
|
||||
p.AllowStandardURLs()
|
||||
p.AllowAttrs("cite").OnElements("blockquote", "q")
|
||||
p.AllowAttrs("href").OnElements("a", "area")
|
||||
p.AllowAttrs("src").OnElements("img")
|
||||
```
|
||||
|
||||
An additional complexity regarding links is the data URI as defined in [RFC2397](http://tools.ietf.org/html/rfc2397). The data URI allows for images to be served inline using this format:
|
||||
|
||||
```html
|
||||
<img src="data:image/webp;base64,UklGRh4AAABXRUJQVlA4TBEAAAAvAAAAAAfQ//73v/+BiOh/AAA=">
|
||||
```
|
||||
|
||||
We have provided a helper to verify the mimetype followed by base64 content of data URIs links:
|
||||
|
||||
```go
|
||||
p.AllowDataURIImages()
|
||||
```
|
||||
|
||||
That helper will enable GIF, JPEG, PNG and WEBP images.
|
||||
|
||||
It should be noted that there is a potential [security](http://palizine.plynt.com/issues/2010Oct/bypass-xss-filters/) [risk](https://capec.mitre.org/data/definitions/244.html) with the use of data URI links. You should only enable data URI links if you already trust the content.
|
||||
|
||||
We also have some features to help deal with user generated content:
|
||||
```go
|
||||
p.AddTargetBlankToFullyQualifiedLinks(true)
|
||||
```
|
||||
|
||||
This will ensure that anchor `<a href="" />` links that are fully qualified (the href destination includes a host name) will get `target="_blank"` added to them.
|
||||
|
||||
Additionally any link that has `target="_blank"` after the policy has been applied will also have the `rel` attribute adjusted to add `noopener`. This means a link may start like `<a href="//host/path"/>` and will end up as `<a href="//host/path" rel="noopener" target="_blank">`. It is important to note that the addition of `noopener` is a security feature and not an issue. There is an unfortunate feature to browsers that a browser window opened as a result of `target="_blank"` can still control the opener (your web page) and this protects against that. The background to this can be found here: [https://dev.to/ben/the-targetblank-vulnerability-by-example](https://dev.to/ben/the-targetblank-vulnerability-by-example)
|
||||
|
||||
### Policy Building Helpers
|
||||
|
||||
We also bundle some helpers to simplify policy building:
|
||||
```go
|
||||
|
||||
// Permits the "dir", "id", "lang", "title" attributes globally
|
||||
p.AllowStandardAttributes()
|
||||
|
||||
// Permits the "img" element and it's standard attributes
|
||||
p.AllowImages()
|
||||
|
||||
// Permits ordered and unordered lists, and also definition lists
|
||||
p.AllowLists()
|
||||
|
||||
// Permits HTML tables and all applicable elements and non-styling attributes
|
||||
p.AllowTables()
|
||||
```
|
||||
|
||||
### Invalid Instructions
|
||||
|
||||
The following are invalid:
|
||||
```go
|
||||
// This does not say where the attributes are allowed, you need to add
|
||||
// .Globally() or .OnElements(...)
|
||||
// This will be ignored without error.
|
||||
p.AllowAttrs("value")
|
||||
|
||||
// This does not say where the attributes are allowed, you need to add
|
||||
// .Globally() or .OnElements(...)
|
||||
// This will be ignored without error.
|
||||
p.AllowAttrs(
|
||||
"type",
|
||||
).Matching(
|
||||
regexp.MustCompile("(?i)^(circle|disc|square|a|A|i|I|1)$"),
|
||||
)
|
||||
```
|
||||
|
||||
Both examples exhibit the same issue, they declare attributes but do not then specify whether they are whitelisted globally or only on specific elements (and which elements). Attributes belong to one or more elements, and the policy needs to declare this.
|
||||
|
||||
## Limitations
|
||||
|
||||
We are not yet including any tools to help whitelist and sanitize CSS. Which means that unless you wish to do the heavy lifting in a single regular expression (inadvisable), **you should not allow the "style" attribute anywhere**.
|
||||
|
||||
It is not the job of bluemonday to fix your bad HTML, it is merely the job of bluemonday to prevent malicious HTML getting through. If you have mismatched HTML elements, or non-conforming nesting of elements, those will remain. But if you have well-structured HTML bluemonday will not break it.
|
||||
|
||||
## TODO
|
||||
|
||||
* Add support for CSS sanitisation to allow some CSS properties based on a whitelist, possibly using the [Gorilla CSS3 scanner](http://www.gorillatoolkit.org/pkg/css/scanner)
|
||||
* Investigate whether devs want to blacklist elements and attributes. This would allow devs to take an existing policy (such as the `bluemonday.UGCPolicy()` ) that encapsulates 90% of what they're looking for but does more than they need, and to remove the extra things they do not want to make it 100% what they want
|
||||
* Investigate whether devs want a validating HTML mode, in which the HTML elements are not just transformed into a balanced tree (every start tag has a closing tag at the correct depth) but also that elements and character data appear only in their allowed context (i.e. that a `table` element isn't a descendent of a `caption`, that `colgroup`, `thead`, `tbody`, `tfoot` and `tr` are permitted, and that character data is not permitted)
|
||||
|
||||
## Development
|
||||
|
||||
If you have cloned this repo you will probably need the dependency:
|
||||
|
||||
`go get golang.org/x/net/html`
|
||||
|
||||
Gophers can use their familiar tools:
|
||||
|
||||
`go build`
|
||||
|
||||
`go test`
|
||||
|
||||
I personally use a Makefile as it spares typing the same args over and over whilst providing consistency for those of us who jump from language to language and enjoy just typing `make` in a project directory and watch magic happen.
|
||||
|
||||
`make` will build, vet, test and install the library.
|
||||
|
||||
`make clean` will remove the library from a *single* `${GOPATH}/pkg` directory tree
|
||||
|
||||
`make test` will run the tests
|
||||
|
||||
`make cover` will run the tests and *open a browser window* with the coverage report
|
||||
|
||||
`make lint` will run golint (install via `go get github.com/golang/lint/golint`)
|
||||
|
||||
## Long term goals
|
||||
|
||||
1. Open the code to adversarial peer review similar to the [Attack Review Ground Rules](https://code.google.com/p/owasp-java-html-sanitizer/wiki/AttackReviewGroundRules)
|
||||
1. Raise funds and pay for an external security review
|
||||
@ -1,12 +0,0 @@
|
||||
/*
|
||||
Package main demonstrates a HTML email cleaner.
|
||||
|
||||
It should be noted that this uses bluemonday to sanitize the HTML but as it
|
||||
preserves the styling of the email this should not be considered a safe or XSS
|
||||
secure approach.
|
||||
|
||||
It does function as a basic demonstration of how to take HTML emails, which are
|
||||
notorious for having inconsistent, obselete and poorly formatted HTML, and to
|
||||
use bluemonday to normalise the output.
|
||||
*/
|
||||
package main
|
||||
@ -1,77 +0,0 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"io/ioutil"
|
||||
"log"
|
||||
"os"
|
||||
"regexp"
|
||||
|
||||
"github.com/microcosm-cc/bluemonday"
|
||||
)
|
||||
|
||||
var (
|
||||
// Color is a valid hex color or name of a web safe color
|
||||
Color = regexp.MustCompile(`(?i)^(#[0-9a-fA-F]{1,6}|black|silver|gray|white|maroon|red|purple|fuchsia|green|lime|olive|yellow|navy|blue|teal|aqua|orange|aliceblue|antiquewhite|aquamarine|azure|beige|bisque|blanchedalmond|blueviolet|brown|burlywood|cadetblue|chartreuse|chocolate|coral|cornflowerblue|cornsilk|crimson|darkblue|darkcyan|darkgoldenrod|darkgray|darkgreen|darkgrey|darkkhaki|darkmagenta|darkolivegreen|darkorange|darkorchid|darkred|darksalmon|darkseagreen|darkslateblue|darkslategray|darkslategrey|darkturquoise|darkviolet|deeppink|deepskyblue|dimgray|dimgrey|dodgerblue|firebrick|floralwhite|forestgreen|gainsboro|ghostwhite|gold|goldenrod|greenyellow|grey|honeydew|hotpink|indianred|indigo|ivory|khaki|lavender|lavenderblush|lawngreen|lemonchiffon|lightblue|lightcoral|lightcyan|lightgoldenrodyellow|lightgray|lightgreen|lightgrey|lightpink|lightsalmon|lightseagreen|lightskyblue|lightslategray|lightslategrey|lightsteelblue|lightyellow|limegreen|linen|mediumaquamarine|mediumblue|mediumorchid|mediumpurple|mediumseagreen|mediumslateblue|mediumspringgreen|mediumturquoise|mediumvioletred|midnightblue|mintcream|mistyrose|moccasin|navajowhite|oldlace|olivedrab|orangered|orchid|palegoldenrod|palegreen|paleturquoise|palevioletred|papayawhip|peachpuff|peru|pink|plum|powderblue|rosybrown|royalblue|saddlebrown|salmon|sandybrown|seagreen|seashell|sienna|skyblue|slateblue|slategray|slategrey|snow|springgreen|steelblue|tan|thistle|tomato|turquoise|violet|wheat|whitesmoke|yellowgreen|rebeccapurple)$`)
|
||||
|
||||
// ButtonType is a button type, or a style type, i.e. "submit"
|
||||
ButtonType = regexp.MustCompile(`(?i)^[a-zA-Z][a-zA-Z-]{1,30}[a-zA-Z]$`)
|
||||
|
||||
// StyleType is the valid type attribute on a style tag in the <head>
|
||||
StyleType = regexp.MustCompile(`(?i)^text\/css$`)
|
||||
)
|
||||
|
||||
func main() {
|
||||
// Define a policy, we are using the UGC policy as a base.
|
||||
p := bluemonday.UGCPolicy()
|
||||
|
||||
// HTML email is often displayed in iframes and needs to preserve core
|
||||
// structure
|
||||
p.AllowDocType(true)
|
||||
p.AllowElements("html", "head", "body", "title")
|
||||
|
||||
// There are not safe, and is only being done here to demonstrate how to
|
||||
// process HTML emails where styling has to be preserved. This is at the
|
||||
// expense of security.
|
||||
p.AllowAttrs("type").Matching(StyleType).OnElements("style")
|
||||
p.AllowAttrs("style").Globally()
|
||||
|
||||
// HTML email frequently contains obselete and basic HTML
|
||||
p.AllowElements("font", "main", "nav", "header", "footer", "kbd", "legend")
|
||||
|
||||
// Need to permit the style tag, and buttons are often found in emails (why?)
|
||||
p.AllowAttrs("type").Matching(ButtonType).OnElements("button")
|
||||
|
||||
// HTML email tends to see the use of obselete spacing and styling attributes
|
||||
p.AllowAttrs("bgcolor", "color").Matching(Color).OnElements("basefont", "font", "hr")
|
||||
p.AllowAttrs("border").Matching(bluemonday.Integer).OnElements("img", "table")
|
||||
p.AllowAttrs("cellpadding", "cellspacing").Matching(bluemonday.Integer).OnElements("table")
|
||||
|
||||
// Allow "class" attributes on all elements
|
||||
p.AllowStyling()
|
||||
|
||||
// Allow images to be embedded via data-uri
|
||||
p.AllowDataURIImages()
|
||||
|
||||
// Add "rel=nofollow" to links
|
||||
p.RequireNoFollowOnLinks(true)
|
||||
p.RequireNoFollowOnFullyQualifiedLinks(true)
|
||||
|
||||
// Open external links in a new window/tab
|
||||
p.AddTargetBlankToFullyQualifiedLinks(true)
|
||||
|
||||
// Read input from stdin so that this is a nice unix utility and can receive
|
||||
// piped input
|
||||
dirty, err := ioutil.ReadAll(os.Stdin)
|
||||
if err != nil {
|
||||
log.Fatal(err)
|
||||
}
|
||||
|
||||
// Apply the policy and write to stdout
|
||||
fmt.Fprint(
|
||||
os.Stdout,
|
||||
p.Sanitize(
|
||||
string(dirty),
|
||||
),
|
||||
)
|
||||
}
|
||||
@ -1,13 +0,0 @@
|
||||
/*
|
||||
Package main demonstrates a simple user generated content sanitizer.
|
||||
|
||||
This is the configuration I use on the sites that I run, it allows a lot of safe
|
||||
HTML that in my case comes from the blackfriday markdown package. As markdown
|
||||
itself allows HTML the UGCPolicy includes most common HTML.
|
||||
|
||||
CSS and JavaScript is excluded (not white-listed), as are form elements and most
|
||||
embedded media that isn't just an image or image map.
|
||||
|
||||
As I'm paranoid, I also do not allow data-uri images and embeds.
|
||||
*/
|
||||
package main
|
||||
@ -1,37 +0,0 @@
|
||||
package main
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"io/ioutil"
|
||||
"log"
|
||||
"os"
|
||||
|
||||
"github.com/microcosm-cc/bluemonday"
|
||||
)
|
||||
|
||||
func main() {
|
||||
// Define a policy, we are using the UGC policy as a base.
|
||||
p := bluemonday.UGCPolicy()
|
||||
|
||||
// Add "rel=nofollow" to links
|
||||
p.RequireNoFollowOnLinks(true)
|
||||
p.RequireNoFollowOnFullyQualifiedLinks(true)
|
||||
|
||||
// Open external links in a new window/tab
|
||||
p.AddTargetBlankToFullyQualifiedLinks(true)
|
||||
|
||||
// Read input from stdin so that this is a nice unix utility and can receive
|
||||
// piped input
|
||||
dirty, err := ioutil.ReadAll(os.Stdin)
|
||||
if err != nil {
|
||||
log.Fatal(err)
|
||||
}
|
||||
|
||||
// Apply the policy and write to stdout
|
||||
fmt.Fprint(
|
||||
os.Stdout,
|
||||
p.Sanitize(
|
||||
string(dirty),
|
||||
),
|
||||
)
|
||||
}
|
||||
104
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/doc.go
generated
vendored
104
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/doc.go
generated
vendored
@ -1,104 +0,0 @@
|
||||
// Copyright (c) 2014, David Kitchen <david@buro9.com>
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without
|
||||
// modification, are permitted provided that the following conditions are met:
|
||||
//
|
||||
// * Redistributions of source code must retain the above copyright notice, this
|
||||
// list of conditions and the following disclaimer.
|
||||
//
|
||||
// * Redistributions in binary form must reproduce the above copyright notice,
|
||||
// this list of conditions and the following disclaimer in the documentation
|
||||
// and/or other materials provided with the distribution.
|
||||
//
|
||||
// * Neither the name of the organisation (Microcosm) nor the names of its
|
||||
// contributors may be used to endorse or promote products derived from
|
||||
// this software without specific prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
|
||||
// AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
|
||||
// IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
|
||||
// DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
|
||||
// FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
|
||||
// DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
|
||||
// SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
|
||||
// CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
|
||||
// OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
|
||||
// OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
/*
|
||||
Package bluemonday provides a way of describing a whitelist of HTML elements
|
||||
and attributes as a policy, and for that policy to be applied to untrusted
|
||||
strings from users that may contain markup. All elements and attributes not on
|
||||
the whitelist will be stripped.
|
||||
|
||||
The default bluemonday.UGCPolicy().Sanitize() turns this:
|
||||
|
||||
Hello <STYLE>.XSS{background-image:url("javascript:alert('XSS')");}</STYLE><A CLASS=XSS></A>World
|
||||
|
||||
Into the more harmless:
|
||||
|
||||
Hello World
|
||||
|
||||
And it turns this:
|
||||
|
||||
<a href="javascript:alert('XSS1')" onmouseover="alert('XSS2')">XSS<a>
|
||||
|
||||
Into this:
|
||||
|
||||
XSS
|
||||
|
||||
Whilst still allowing this:
|
||||
|
||||
<a href="http://www.google.com/">
|
||||
<img src="https://ssl.gstatic.com/accounts/ui/logo_2x.png"/>
|
||||
</a>
|
||||
|
||||
To pass through mostly unaltered (it gained a rel="nofollow"):
|
||||
|
||||
<a href="http://www.google.com/" rel="nofollow">
|
||||
<img src="https://ssl.gstatic.com/accounts/ui/logo_2x.png"/>
|
||||
</a>
|
||||
|
||||
The primary purpose of bluemonday is to take potentially unsafe user generated
|
||||
content (from things like Markdown, HTML WYSIWYG tools, etc) and make it safe
|
||||
for you to put on your website.
|
||||
|
||||
It protects sites against XSS (http://en.wikipedia.org/wiki/Cross-site_scripting)
|
||||
and other malicious content that a user interface may deliver. There are many
|
||||
vectors for an XSS attack (https://www.owasp.org/index.php/XSS_Filter_Evasion_Cheat_Sheet)
|
||||
and the safest thing to do is to sanitize user input against a known safe list
|
||||
of HTML elements and attributes.
|
||||
|
||||
Note: You should always run bluemonday after any other processing.
|
||||
|
||||
If you use blackfriday (https://github.com/russross/blackfriday) or
|
||||
Pandoc (http://johnmacfarlane.net/pandoc/) then bluemonday should be run after
|
||||
these steps. This ensures that no insecure HTML is introduced later in your
|
||||
process.
|
||||
|
||||
bluemonday is heavily inspired by both the OWASP Java HTML Sanitizer
|
||||
(https://code.google.com/p/owasp-java-html-sanitizer/) and the HTML Purifier
|
||||
(http://htmlpurifier.org/).
|
||||
|
||||
We ship two default policies, one is bluemonday.StrictPolicy() and can be
|
||||
thought of as equivalent to stripping all HTML elements and their attributes as
|
||||
it has nothing on it's whitelist.
|
||||
|
||||
The other is bluemonday.UGCPolicy() and allows a broad selection of HTML
|
||||
elements and attributes that are safe for user generated content. Note that
|
||||
this policy does not whitelist iframes, object, embed, styles, script, etc.
|
||||
|
||||
The essence of building a policy is to determine which HTML elements and
|
||||
attributes are considered safe for your scenario. OWASP provide an XSS
|
||||
prevention cheat sheet ( https://www.google.com/search?q=xss+prevention+cheat+sheet )
|
||||
to help explain the risks, but essentially:
|
||||
|
||||
1. Avoid whitelisting anything other than plain HTML elements
|
||||
2. Avoid whitelisting `script`, `style`, `iframe`, `object`, `embed`, `base`
|
||||
elements
|
||||
3. Avoid whitelisting anything other than plain HTML elements with simple
|
||||
values that you can match to a regexp
|
||||
*/
|
||||
package bluemonday
|
||||
240
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/example_test.go
generated
vendored
240
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/example_test.go
generated
vendored
@ -1,240 +0,0 @@
|
||||
// Copyright (c) 2014, David Kitchen <david@buro9.com>
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without
|
||||
// modification, are permitted provided that the following conditions are met:
|
||||
//
|
||||
// * Redistributions of source code must retain the above copyright notice, this
|
||||
// list of conditions and the following disclaimer.
|
||||
//
|
||||
// * Redistributions in binary form must reproduce the above copyright notice,
|
||||
// this list of conditions and the following disclaimer in the documentation
|
||||
// and/or other materials provided with the distribution.
|
||||
//
|
||||
// * Neither the name of the organisation (Microcosm) nor the names of its
|
||||
// contributors may be used to endorse or promote products derived from
|
||||
// this software without specific prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
|
||||
// AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
|
||||
// IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
|
||||
// DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
|
||||
// FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
|
||||
// DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
|
||||
// SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
|
||||
// CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
|
||||
// OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
|
||||
// OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
package bluemonday_test
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"regexp"
|
||||
"strings"
|
||||
|
||||
"github.com/microcosm-cc/bluemonday"
|
||||
)
|
||||
|
||||
func Example() {
|
||||
// Create a new policy
|
||||
p := bluemonday.NewPolicy()
|
||||
|
||||
// Add elements to a policy without attributes
|
||||
p.AllowElements("b", "strong")
|
||||
|
||||
// Add elements as a virtue of adding an attribute
|
||||
p.AllowAttrs("nowrap").OnElements("td", "th")
|
||||
|
||||
// Attributes can either be added to all elements
|
||||
p.AllowAttrs("dir").Globally()
|
||||
|
||||
//Or attributes can be added to specific elements
|
||||
p.AllowAttrs("value").OnElements("li")
|
||||
|
||||
// It is ALWAYS recommended that an attribute be made to match a pattern
|
||||
// XSS in HTML attributes is a very easy attack vector
|
||||
|
||||
// \p{L} matches unicode letters, \p{N} matches unicode numbers
|
||||
p.AllowAttrs("title").Matching(regexp.MustCompile(`[\p{L}\p{N}\s\-_',:\[\]!\./\\\(\)&]*`)).Globally()
|
||||
|
||||
// You can stop at any time and call .Sanitize()
|
||||
|
||||
// Assumes that string htmlIn was passed in from a HTTP POST and contains
|
||||
// untrusted user generated content
|
||||
htmlIn := `untrusted user generated content <body onload="alert('XSS')">`
|
||||
fmt.Println(p.Sanitize(htmlIn))
|
||||
|
||||
// And you can take any existing policy and extend it
|
||||
p = bluemonday.UGCPolicy()
|
||||
p.AllowElements("fieldset", "select", "option")
|
||||
|
||||
// Links are complex beasts and one of the biggest attack vectors for
|
||||
// malicious content so we have included features specifically to help here.
|
||||
|
||||
// This is not recommended:
|
||||
p = bluemonday.NewPolicy()
|
||||
p.AllowAttrs("href").Matching(regexp.MustCompile(`(?i)mailto|https?`)).OnElements("a")
|
||||
|
||||
// The regexp is insufficient in this case to have prevented a malformed
|
||||
// value doing something unexpected.
|
||||
|
||||
// This will ensure that URLs are not considered invalid by Go's net/url
|
||||
// package.
|
||||
p.RequireParseableURLs(true)
|
||||
|
||||
// If you have enabled parseable URLs then the following option will allow
|
||||
// relative URLs. By default this is disabled and will prevent all local and
|
||||
// schema relative URLs (i.e. `href="//www.google.com"` is schema relative).
|
||||
p.AllowRelativeURLs(true)
|
||||
|
||||
// If you have enabled parseable URLs then you can whitelist the schemas
|
||||
// that are permitted. Bear in mind that allowing relative URLs in the above
|
||||
// option allows for blank schemas.
|
||||
p.AllowURLSchemes("mailto", "http", "https")
|
||||
|
||||
// Regardless of whether you have enabled parseable URLs, you can force all
|
||||
// URLs to have a rel="nofollow" attribute. This will be added if it does
|
||||
// not exist.
|
||||
|
||||
// This applies to "a" "area" "link" elements that have a "href" attribute
|
||||
p.RequireNoFollowOnLinks(true)
|
||||
|
||||
// We provide a convenience function that applies all of the above, but you
|
||||
// will still need to whitelist the linkable elements:
|
||||
p = bluemonday.NewPolicy()
|
||||
p.AllowStandardURLs()
|
||||
p.AllowAttrs("cite").OnElements("blockquote")
|
||||
p.AllowAttrs("href").OnElements("a", "area")
|
||||
p.AllowAttrs("src").OnElements("img")
|
||||
|
||||
// Policy Building Helpers
|
||||
|
||||
// If you've got this far and you're bored already, we also bundle some
|
||||
// other convenience functions
|
||||
p = bluemonday.NewPolicy()
|
||||
p.AllowStandardAttributes()
|
||||
p.AllowImages()
|
||||
p.AllowLists()
|
||||
p.AllowTables()
|
||||
}
|
||||
|
||||
func ExampleNewPolicy() {
|
||||
// NewPolicy is a blank policy and we need to explicitly whitelist anything
|
||||
// that we wish to allow through
|
||||
p := bluemonday.NewPolicy()
|
||||
|
||||
// We ensure any URLs are parseable and have rel="nofollow" where applicable
|
||||
p.AllowStandardURLs()
|
||||
|
||||
// AllowStandardURLs already ensures that the href will be valid, and so we
|
||||
// can skip the .Matching()
|
||||
p.AllowAttrs("href").OnElements("a")
|
||||
|
||||
// We allow paragraphs too
|
||||
p.AllowElements("p")
|
||||
|
||||
html := p.Sanitize(
|
||||
`<p><a onblur="alert(secret)" href="http://www.google.com">Google</a></p>`,
|
||||
)
|
||||
|
||||
fmt.Println(html)
|
||||
|
||||
// Output:
|
||||
//<p><a href="http://www.google.com" rel="nofollow">Google</a></p>
|
||||
}
|
||||
|
||||
func ExampleStrictPolicy() {
|
||||
// StrictPolicy is equivalent to NewPolicy and as nothing else is declared
|
||||
// we are stripping all elements (and their attributes)
|
||||
p := bluemonday.StrictPolicy()
|
||||
|
||||
html := p.Sanitize(
|
||||
`Goodbye <a onblur="alert(secret)" href="http://en.wikipedia.org/wiki/Goodbye_Cruel_World_(Pink_Floyd_song)">Cruel</a> World`,
|
||||
)
|
||||
|
||||
fmt.Println(html)
|
||||
|
||||
// Output:
|
||||
//Goodbye Cruel World
|
||||
}
|
||||
|
||||
func ExampleUGCPolicy() {
|
||||
// UGCPolicy is a convenience policy for user generated content.
|
||||
p := bluemonday.UGCPolicy()
|
||||
|
||||
html := p.Sanitize(
|
||||
`<a onblur="alert(secret)" href="http://www.google.com">Google</a>`,
|
||||
)
|
||||
|
||||
fmt.Println(html)
|
||||
|
||||
// Output:
|
||||
//<a href="http://www.google.com" rel="nofollow">Google</a>
|
||||
}
|
||||
|
||||
func ExamplePolicy_AllowAttrs() {
|
||||
p := bluemonday.NewPolicy()
|
||||
|
||||
// Allow the 'title' attribute on every HTML element that has been
|
||||
// whitelisted
|
||||
p.AllowAttrs("title").Matching(bluemonday.Paragraph).Globally()
|
||||
|
||||
// Allow the 'abbr' attribute on only the 'td' and 'th' elements.
|
||||
p.AllowAttrs("abbr").Matching(bluemonday.Paragraph).OnElements("td", "th")
|
||||
|
||||
// Allow the 'colspan' and 'rowspan' attributes, matching a positive integer
|
||||
// pattern, on only the 'td' and 'th' elements.
|
||||
p.AllowAttrs("colspan", "rowspan").Matching(
|
||||
bluemonday.Integer,
|
||||
).OnElements("td", "th")
|
||||
}
|
||||
|
||||
func ExamplePolicy_AllowElements() {
|
||||
p := bluemonday.NewPolicy()
|
||||
|
||||
// Allow styling elements without attributes
|
||||
p.AllowElements("br", "div", "hr", "p", "span")
|
||||
}
|
||||
|
||||
func ExamplePolicy_Sanitize() {
|
||||
// UGCPolicy is a convenience policy for user generated content.
|
||||
p := bluemonday.UGCPolicy()
|
||||
|
||||
// string in, string out
|
||||
html := p.Sanitize(`<a onblur="alert(secret)" href="http://www.google.com">Google</a>`)
|
||||
|
||||
fmt.Println(html)
|
||||
|
||||
// Output:
|
||||
//<a href="http://www.google.com" rel="nofollow">Google</a>
|
||||
}
|
||||
|
||||
func ExamplePolicy_SanitizeBytes() {
|
||||
// UGCPolicy is a convenience policy for user generated content.
|
||||
p := bluemonday.UGCPolicy()
|
||||
|
||||
// []byte in, []byte out
|
||||
b := []byte(`<a onblur="alert(secret)" href="http://www.google.com">Google</a>`)
|
||||
b = p.SanitizeBytes(b)
|
||||
|
||||
fmt.Println(string(b))
|
||||
|
||||
// Output:
|
||||
//<a href="http://www.google.com" rel="nofollow">Google</a>
|
||||
}
|
||||
|
||||
func ExamplePolicy_SanitizeReader() {
|
||||
// UGCPolicy is a convenience policy for user generated content.
|
||||
p := bluemonday.UGCPolicy()
|
||||
|
||||
// io.Reader in, bytes.Buffer out
|
||||
r := strings.NewReader(`<a onblur="alert(secret)" href="http://www.google.com">Google</a>`)
|
||||
buf := p.SanitizeReader(r)
|
||||
|
||||
fmt.Println(buf.String())
|
||||
|
||||
// Output:
|
||||
//<a href="http://www.google.com" rel="nofollow">Google</a>
|
||||
}
|
||||
297
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/helpers.go
generated
vendored
297
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/helpers.go
generated
vendored
@ -1,297 +0,0 @@
|
||||
// Copyright (c) 2014, David Kitchen <david@buro9.com>
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without
|
||||
// modification, are permitted provided that the following conditions are met:
|
||||
//
|
||||
// * Redistributions of source code must retain the above copyright notice, this
|
||||
// list of conditions and the following disclaimer.
|
||||
//
|
||||
// * Redistributions in binary form must reproduce the above copyright notice,
|
||||
// this list of conditions and the following disclaimer in the documentation
|
||||
// and/or other materials provided with the distribution.
|
||||
//
|
||||
// * Neither the name of the organisation (Microcosm) nor the names of its
|
||||
// contributors may be used to endorse or promote products derived from
|
||||
// this software without specific prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
|
||||
// AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
|
||||
// IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
|
||||
// DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
|
||||
// FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
|
||||
// DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
|
||||
// SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
|
||||
// CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
|
||||
// OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
|
||||
// OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
package bluemonday
|
||||
|
||||
import (
|
||||
"encoding/base64"
|
||||
"net/url"
|
||||
"regexp"
|
||||
)
|
||||
|
||||
// A selection of regular expressions that can be used as .Matching() rules on
|
||||
// HTML attributes.
|
||||
var (
|
||||
// CellAlign handles the `align` attribute
|
||||
// https://developer.mozilla.org/en-US/docs/Web/HTML/Element/td#attr-align
|
||||
CellAlign = regexp.MustCompile(`(?i)^(center|justify|left|right|char)$`)
|
||||
|
||||
// CellVerticalAlign handles the `valign` attribute
|
||||
// https://developer.mozilla.org/en-US/docs/Web/HTML/Element/td#attr-valign
|
||||
CellVerticalAlign = regexp.MustCompile(`(?i)^(baseline|bottom|middle|top)$`)
|
||||
|
||||
// Direction handles the `dir` attribute
|
||||
// https://developer.mozilla.org/en-US/docs/Web/HTML/Element/bdo#attr-dir
|
||||
Direction = regexp.MustCompile(`(?i)^(rtl|ltr)$`)
|
||||
|
||||
// ImageAlign handles the `align` attribute on the `image` tag
|
||||
// http://www.w3.org/MarkUp/Test/Img/imgtest.html
|
||||
ImageAlign = regexp.MustCompile(
|
||||
`(?i)^(left|right|top|texttop|middle|absmiddle|baseline|bottom|absbottom)$`,
|
||||
)
|
||||
|
||||
// Integer describes whole positive integers (including 0) used in places
|
||||
// like td.colspan
|
||||
// https://developer.mozilla.org/en-US/docs/Web/HTML/Element/td#attr-colspan
|
||||
Integer = regexp.MustCompile(`^[0-9]+$`)
|
||||
|
||||
// ISO8601 according to the W3 group is only a subset of the ISO8601
|
||||
// standard: http://www.w3.org/TR/NOTE-datetime
|
||||
//
|
||||
// Used in places like time.datetime
|
||||
// https://developer.mozilla.org/en-US/docs/Web/HTML/Element/time#attr-datetime
|
||||
//
|
||||
// Matches patterns:
|
||||
// Year:
|
||||
// YYYY (eg 1997)
|
||||
// Year and month:
|
||||
// YYYY-MM (eg 1997-07)
|
||||
// Complete date:
|
||||
// YYYY-MM-DD (eg 1997-07-16)
|
||||
// Complete date plus hours and minutes:
|
||||
// YYYY-MM-DDThh:mmTZD (eg 1997-07-16T19:20+01:00)
|
||||
// Complete date plus hours, minutes and seconds:
|
||||
// YYYY-MM-DDThh:mm:ssTZD (eg 1997-07-16T19:20:30+01:00)
|
||||
// Complete date plus hours, minutes, seconds and a decimal fraction of a
|
||||
// second
|
||||
// YYYY-MM-DDThh:mm:ss.sTZD (eg 1997-07-16T19:20:30.45+01:00)
|
||||
ISO8601 = regexp.MustCompile(
|
||||
`^[0-9]{4}(-[0-9]{2}(-[0-9]{2}([ T][0-9]{2}(:[0-9]{2}){1,2}(.[0-9]{1,6})` +
|
||||
`?Z?([\+-][0-9]{2}:[0-9]{2})?)?)?)?$`,
|
||||
)
|
||||
|
||||
// ListType encapsulates the common value as well as the latest spec
|
||||
// values for lists
|
||||
// https://developer.mozilla.org/en-US/docs/Web/HTML/Element/ol#attr-type
|
||||
ListType = regexp.MustCompile(`(?i)^(circle|disc|square|a|A|i|I|1)$`)
|
||||
|
||||
// SpaceSeparatedTokens is used in places like `a.rel` and the common attribute
|
||||
// `class` which both contain space delimited lists of data tokens
|
||||
// http://www.w3.org/TR/html-markup/datatypes.html#common.data.tokens-def
|
||||
// Regexp: \p{L} matches unicode letters, \p{N} matches unicode numbers
|
||||
SpaceSeparatedTokens = regexp.MustCompile(`^([\s\p{L}\p{N}_-]+)$`)
|
||||
|
||||
// Number is a double value used on HTML5 meter and progress elements
|
||||
// http://www.whatwg.org/specs/web-apps/current-work/multipage/the-button-element.html#the-meter-element
|
||||
Number = regexp.MustCompile(`^[-+]?[0-9]*\.?[0-9]+([eE][-+]?[0-9]+)?$`)
|
||||
|
||||
// NumberOrPercent is used predominantly as units of measurement in width
|
||||
// and height attributes
|
||||
// https://developer.mozilla.org/en-US/docs/Web/HTML/Element/img#attr-height
|
||||
NumberOrPercent = regexp.MustCompile(`^[0-9]+[%]?$`)
|
||||
|
||||
// Paragraph of text in an attribute such as *.'title', img.alt, etc
|
||||
// https://developer.mozilla.org/en-US/docs/Web/HTML/Global_attributes#attr-title
|
||||
// Note that we are not allowing chars that could close tags like '>'
|
||||
Paragraph = regexp.MustCompile(`^[\p{L}\p{N}\s\-_',\[\]!\./\\\(\)]*$`)
|
||||
|
||||
// dataURIImagePrefix is used by AllowDataURIImages to define the acceptable
|
||||
// prefix of data URIs that contain common web image formats.
|
||||
//
|
||||
// This is not exported as it's not useful by itself, and only has value
|
||||
// within the AllowDataURIImages func
|
||||
dataURIImagePrefix = regexp.MustCompile(
|
||||
`^image/(gif|jpeg|png|webp);base64,`,
|
||||
)
|
||||
)
|
||||
|
||||
// AllowStandardURLs is a convenience function that will enable rel="nofollow"
|
||||
// on "a", "area" and "link" (if you have allowed those elements) and will
|
||||
// ensure that the URL values are parseable and either relative or belong to the
|
||||
// "mailto", "http", or "https" schemes
|
||||
func (p *Policy) AllowStandardURLs() {
|
||||
// URLs must be parseable by net/url.Parse()
|
||||
p.RequireParseableURLs(true)
|
||||
|
||||
// !url.IsAbs() is permitted
|
||||
p.AllowRelativeURLs(true)
|
||||
|
||||
// Most common URL schemes only
|
||||
p.AllowURLSchemes("mailto", "http", "https")
|
||||
|
||||
// For all anchors we will add rel="nofollow" if it does not already exist
|
||||
// This applies to "a" "area" "link"
|
||||
p.RequireNoFollowOnLinks(true)
|
||||
}
|
||||
|
||||
// AllowStandardAttributes will enable "id", "title" and the language specific
|
||||
// attributes "dir" and "lang" on all elements that are whitelisted
|
||||
func (p *Policy) AllowStandardAttributes() {
|
||||
// "dir" "lang" are permitted as both language attributes affect charsets
|
||||
// and direction of text.
|
||||
p.AllowAttrs("dir").Matching(Direction).Globally()
|
||||
p.AllowAttrs(
|
||||
"lang",
|
||||
).Matching(regexp.MustCompile(`[a-zA-Z]{2,20}`)).Globally()
|
||||
|
||||
// "id" is permitted. This is pretty much as some HTML elements require this
|
||||
// to work well ("dfn" is an example of a "id" being value)
|
||||
// This does create a risk that JavaScript and CSS within your web page
|
||||
// might identify the wrong elements. Ensure that you select things
|
||||
// accurately
|
||||
p.AllowAttrs("id").Matching(
|
||||
regexp.MustCompile(`[a-zA-Z0-9\:\-_\.]+`),
|
||||
).Globally()
|
||||
|
||||
// "title" is permitted as it improves accessibility.
|
||||
p.AllowAttrs("title").Matching(Paragraph).Globally()
|
||||
}
|
||||
|
||||
// AllowStyling presently enables the class attribute globally.
|
||||
//
|
||||
// Note: When bluemonday ships a CSS parser and we can safely sanitise that,
|
||||
// this will also allow sanitized styling of elements via the style attribute.
|
||||
func (p *Policy) AllowStyling() {
|
||||
|
||||
// "class" is permitted globally
|
||||
p.AllowAttrs("class").Matching(SpaceSeparatedTokens).Globally()
|
||||
}
|
||||
|
||||
// AllowImages enables the img element and some popular attributes. It will also
|
||||
// ensure that URL values are parseable. This helper does not enable data URI
|
||||
// images, for that you should also use the AllowDataURIImages() helper.
|
||||
func (p *Policy) AllowImages() {
|
||||
|
||||
// "img" is permitted
|
||||
p.AllowAttrs("align").Matching(ImageAlign).OnElements("img")
|
||||
p.AllowAttrs("alt").Matching(Paragraph).OnElements("img")
|
||||
p.AllowAttrs("height", "width").Matching(NumberOrPercent).OnElements("img")
|
||||
|
||||
// Standard URLs enabled
|
||||
p.AllowStandardURLs()
|
||||
p.AllowAttrs("src").OnElements("img")
|
||||
}
|
||||
|
||||
// AllowDataURIImages permits the use of inline images defined in RFC2397
|
||||
// http://tools.ietf.org/html/rfc2397
|
||||
// http://en.wikipedia.org/wiki/Data_URI_scheme
|
||||
//
|
||||
// Images must have a mimetype matching:
|
||||
// image/gif
|
||||
// image/jpeg
|
||||
// image/png
|
||||
// image/webp
|
||||
//
|
||||
// NOTE: There is a potential security risk to allowing data URIs and you should
|
||||
// only permit them on content you already trust.
|
||||
// http://palizine.plynt.com/issues/2010Oct/bypass-xss-filters/
|
||||
// https://capec.mitre.org/data/definitions/244.html
|
||||
func (p *Policy) AllowDataURIImages() {
|
||||
|
||||
// URLs must be parseable by net/url.Parse()
|
||||
p.RequireParseableURLs(true)
|
||||
|
||||
// Supply a function to validate images contained within data URI
|
||||
p.AllowURLSchemeWithCustomPolicy(
|
||||
"data",
|
||||
func(url *url.URL) (allowUrl bool) {
|
||||
if url.RawQuery != "" || url.Fragment != "" {
|
||||
return false
|
||||
}
|
||||
|
||||
matched := dataURIImagePrefix.FindString(url.Opaque)
|
||||
if matched == "" {
|
||||
return false
|
||||
}
|
||||
|
||||
_, err := base64.StdEncoding.DecodeString(url.Opaque[len(matched):])
|
||||
if err != nil {
|
||||
return false
|
||||
}
|
||||
|
||||
return true
|
||||
},
|
||||
)
|
||||
}
|
||||
|
||||
// AllowLists will enabled ordered and unordered lists, as well as definition
|
||||
// lists
|
||||
func (p *Policy) AllowLists() {
|
||||
// "ol" "ul" are permitted
|
||||
p.AllowAttrs("type").Matching(ListType).OnElements("ol", "ul")
|
||||
|
||||
// "li" is permitted
|
||||
p.AllowAttrs("type").Matching(ListType).OnElements("li")
|
||||
p.AllowAttrs("value").Matching(Integer).OnElements("li")
|
||||
|
||||
// "dl" "dt" "dd" are permitted
|
||||
p.AllowElements("dl", "dt", "dd")
|
||||
}
|
||||
|
||||
// AllowTables will enable a rich set of elements and attributes to describe
|
||||
// HTML tables
|
||||
func (p *Policy) AllowTables() {
|
||||
|
||||
// "table" is permitted
|
||||
p.AllowAttrs("height", "width").Matching(NumberOrPercent).OnElements("table")
|
||||
p.AllowAttrs("summary").Matching(Paragraph).OnElements("table")
|
||||
|
||||
// "caption" is permitted
|
||||
p.AllowElements("caption")
|
||||
|
||||
// "col" "colgroup" are permitted
|
||||
p.AllowAttrs("align").Matching(CellAlign).OnElements("col", "colgroup")
|
||||
p.AllowAttrs("height", "width").Matching(
|
||||
NumberOrPercent,
|
||||
).OnElements("col", "colgroup")
|
||||
p.AllowAttrs("span").Matching(Integer).OnElements("colgroup", "col")
|
||||
p.AllowAttrs("valign").Matching(
|
||||
CellVerticalAlign,
|
||||
).OnElements("col", "colgroup")
|
||||
|
||||
// "thead" "tr" are permitted
|
||||
p.AllowAttrs("align").Matching(CellAlign).OnElements("thead", "tr")
|
||||
p.AllowAttrs("valign").Matching(CellVerticalAlign).OnElements("thead", "tr")
|
||||
|
||||
// "td" "th" are permitted
|
||||
p.AllowAttrs("abbr").Matching(Paragraph).OnElements("td", "th")
|
||||
p.AllowAttrs("align").Matching(CellAlign).OnElements("td", "th")
|
||||
p.AllowAttrs("colspan", "rowspan").Matching(Integer).OnElements("td", "th")
|
||||
p.AllowAttrs("headers").Matching(
|
||||
SpaceSeparatedTokens,
|
||||
).OnElements("td", "th")
|
||||
p.AllowAttrs("height", "width").Matching(
|
||||
NumberOrPercent,
|
||||
).OnElements("td", "th")
|
||||
p.AllowAttrs(
|
||||
"scope",
|
||||
).Matching(
|
||||
regexp.MustCompile(`(?i)(?:row|col)(?:group)?`),
|
||||
).OnElements("td", "th")
|
||||
p.AllowAttrs("valign").Matching(CellVerticalAlign).OnElements("td", "th")
|
||||
p.AllowAttrs("nowrap").Matching(
|
||||
regexp.MustCompile(`(?i)|nowrap`),
|
||||
).OnElements("td", "th")
|
||||
|
||||
// "tbody" "tfoot"
|
||||
p.AllowAttrs("align").Matching(CellAlign).OnElements("tbody", "tfoot")
|
||||
p.AllowAttrs("valign").Matching(
|
||||
CellVerticalAlign,
|
||||
).OnElements("tbody", "tfoot")
|
||||
}
|
||||
377
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/helpers_test.go
generated
vendored
377
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/helpers_test.go
generated
vendored
File diff suppressed because one or more lines are too long
253
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/policies.go
generated
vendored
253
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/policies.go
generated
vendored
@ -1,253 +0,0 @@
|
||||
// Copyright (c) 2014, David Kitchen <david@buro9.com>
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without
|
||||
// modification, are permitted provided that the following conditions are met:
|
||||
//
|
||||
// * Redistributions of source code must retain the above copyright notice, this
|
||||
// list of conditions and the following disclaimer.
|
||||
//
|
||||
// * Redistributions in binary form must reproduce the above copyright notice,
|
||||
// this list of conditions and the following disclaimer in the documentation
|
||||
// and/or other materials provided with the distribution.
|
||||
//
|
||||
// * Neither the name of the organisation (Microcosm) nor the names of its
|
||||
// contributors may be used to endorse or promote products derived from
|
||||
// this software without specific prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
|
||||
// AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
|
||||
// IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
|
||||
// DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
|
||||
// FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
|
||||
// DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
|
||||
// SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
|
||||
// CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
|
||||
// OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
|
||||
// OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
package bluemonday
|
||||
|
||||
import (
|
||||
"regexp"
|
||||
)
|
||||
|
||||
// StrictPolicy returns an empty policy, which will effectively strip all HTML
|
||||
// elements and their attributes from a document.
|
||||
func StrictPolicy() *Policy {
|
||||
return NewPolicy()
|
||||
}
|
||||
|
||||
// StripTagsPolicy is DEPRECATED. Use StrictPolicy instead.
|
||||
func StripTagsPolicy() *Policy {
|
||||
return StrictPolicy()
|
||||
}
|
||||
|
||||
// UGCPolicy returns a policy aimed at user generated content that is a result
|
||||
// of HTML WYSIWYG tools and Markdown conversions.
|
||||
//
|
||||
// This is expected to be a fairly rich document where as much markup as
|
||||
// possible should be retained. Markdown permits raw HTML so we are basically
|
||||
// providing a policy to sanitise HTML5 documents safely but with the
|
||||
// least intrusion on the formatting expectations of the user.
|
||||
func UGCPolicy() *Policy {
|
||||
|
||||
p := NewPolicy()
|
||||
|
||||
///////////////////////
|
||||
// Global attributes //
|
||||
///////////////////////
|
||||
|
||||
// "class" is not permitted as we are not allowing users to style their own
|
||||
// content
|
||||
|
||||
p.AllowStandardAttributes()
|
||||
|
||||
//////////////////////////////
|
||||
// Global URL format policy //
|
||||
//////////////////////////////
|
||||
|
||||
p.AllowStandardURLs()
|
||||
|
||||
////////////////////////////////
|
||||
// Declarations and structure //
|
||||
////////////////////////////////
|
||||
|
||||
// "xml" "xslt" "DOCTYPE" "html" "head" are not permitted as we are
|
||||
// expecting user generated content to be a fragment of HTML and not a full
|
||||
// document.
|
||||
|
||||
//////////////////////////
|
||||
// Sectioning root tags //
|
||||
//////////////////////////
|
||||
|
||||
// "article" and "aside" are permitted and takes no attributes
|
||||
p.AllowElements("article", "aside")
|
||||
|
||||
// "body" is not permitted as we are expecting user generated content to be a fragment
|
||||
// of HTML and not a full document.
|
||||
|
||||
// "details" is permitted, including the "open" attribute which can either
|
||||
// be blank or the value "open".
|
||||
p.AllowAttrs(
|
||||
"open",
|
||||
).Matching(regexp.MustCompile(`(?i)^(|open)$`)).OnElements("details")
|
||||
|
||||
// "fieldset" is not permitted as we are not allowing forms to be created.
|
||||
|
||||
// "figure" is permitted and takes no attributes
|
||||
p.AllowElements("figure")
|
||||
|
||||
// "nav" is not permitted as it is assumed that the site (and not the user)
|
||||
// has defined navigation elements
|
||||
|
||||
// "section" is permitted and takes no attributes
|
||||
p.AllowElements("section")
|
||||
|
||||
// "summary" is permitted and takes no attributes
|
||||
p.AllowElements("summary")
|
||||
|
||||
//////////////////////////
|
||||
// Headings and footers //
|
||||
//////////////////////////
|
||||
|
||||
// "footer" is not permitted as we expect user content to be a fragment and
|
||||
// not structural to this extent
|
||||
|
||||
// "h1" through "h6" are permitted and take no attributes
|
||||
p.AllowElements("h1", "h2", "h3", "h4", "h5", "h6")
|
||||
|
||||
// "header" is not permitted as we expect user content to be a fragment and
|
||||
// not structural to this extent
|
||||
|
||||
// "hgroup" is permitted and takes no attributes
|
||||
p.AllowElements("hgroup")
|
||||
|
||||
/////////////////////////////////////
|
||||
// Content grouping and separating //
|
||||
/////////////////////////////////////
|
||||
|
||||
// "blockquote" is permitted, including the "cite" attribute which must be
|
||||
// a standard URL.
|
||||
p.AllowAttrs("cite").OnElements("blockquote")
|
||||
|
||||
// "br" "div" "hr" "p" "span" "wbr" are permitted and take no attributes
|
||||
p.AllowElements("br", "div", "hr", "p", "span", "wbr")
|
||||
|
||||
///////////
|
||||
// Links //
|
||||
///////////
|
||||
|
||||
// "a" is permitted
|
||||
p.AllowAttrs("href").OnElements("a")
|
||||
|
||||
// "area" is permitted along with the attributes that map image maps work
|
||||
p.AllowAttrs("name").Matching(
|
||||
regexp.MustCompile(`^([\p{L}\p{N}_-]+)$`),
|
||||
).OnElements("map")
|
||||
p.AllowAttrs("alt").Matching(Paragraph).OnElements("area")
|
||||
p.AllowAttrs("coords").Matching(
|
||||
regexp.MustCompile(`^([0-9]+,)+[0-9]+$`),
|
||||
).OnElements("area")
|
||||
p.AllowAttrs("href").OnElements("area")
|
||||
p.AllowAttrs("rel").Matching(SpaceSeparatedTokens).OnElements("area")
|
||||
p.AllowAttrs("shape").Matching(
|
||||
regexp.MustCompile(`(?i)^(default|circle|rect|poly)$`),
|
||||
).OnElements("area")
|
||||
p.AllowAttrs("usemap").Matching(
|
||||
regexp.MustCompile(`(?i)^#[\p{L}\p{N}_-]+$`),
|
||||
).OnElements("img")
|
||||
|
||||
// "link" is not permitted
|
||||
|
||||
/////////////////////
|
||||
// Phrase elements //
|
||||
/////////////////////
|
||||
|
||||
// The following are all inline phrasing elements
|
||||
p.AllowElements("abbr", "acronym", "cite", "code", "dfn", "em",
|
||||
"figcaption", "mark", "s", "samp", "strong", "sub", "sup", "var")
|
||||
|
||||
// "q" is permitted and "cite" is a URL and handled by URL policies
|
||||
p.AllowAttrs("cite").OnElements("q")
|
||||
|
||||
// "time" is permitted
|
||||
p.AllowAttrs("datetime").Matching(ISO8601).OnElements("time")
|
||||
|
||||
////////////////////
|
||||
// Style elements //
|
||||
////////////////////
|
||||
|
||||
// block and inline elements that impart no semantic meaning but style the
|
||||
// document
|
||||
p.AllowElements("b", "i", "pre", "small", "strike", "tt", "u")
|
||||
|
||||
// "style" is not permitted as we are not yet sanitising CSS and it is an
|
||||
// XSS attack vector
|
||||
|
||||
//////////////////////
|
||||
// HTML5 Formatting //
|
||||
//////////////////////
|
||||
|
||||
// "bdi" "bdo" are permitted
|
||||
p.AllowAttrs("dir").Matching(Direction).OnElements("bdi", "bdo")
|
||||
|
||||
// "rp" "rt" "ruby" are permitted
|
||||
p.AllowElements("rp", "rt", "ruby")
|
||||
|
||||
///////////////////////////
|
||||
// HTML5 Change tracking //
|
||||
///////////////////////////
|
||||
|
||||
// "del" "ins" are permitted
|
||||
p.AllowAttrs("cite").Matching(Paragraph).OnElements("del", "ins")
|
||||
p.AllowAttrs("datetime").Matching(ISO8601).OnElements("del", "ins")
|
||||
|
||||
///////////
|
||||
// Lists //
|
||||
///////////
|
||||
|
||||
p.AllowLists()
|
||||
|
||||
////////////
|
||||
// Tables //
|
||||
////////////
|
||||
|
||||
p.AllowTables()
|
||||
|
||||
///////////
|
||||
// Forms //
|
||||
///////////
|
||||
|
||||
// By and large, forms are not permitted. However there are some form
|
||||
// elements that can be used to present data, and we do permit those
|
||||
//
|
||||
// "button" "fieldset" "input" "keygen" "label" "output" "select" "datalist"
|
||||
// "textarea" "optgroup" "option" are all not permitted
|
||||
|
||||
// "meter" is permitted
|
||||
p.AllowAttrs(
|
||||
"value",
|
||||
"min",
|
||||
"max",
|
||||
"low",
|
||||
"high",
|
||||
"optimum",
|
||||
).Matching(Number).OnElements("meter")
|
||||
|
||||
// "progress" is permitted
|
||||
p.AllowAttrs("value", "max").Matching(Number).OnElements("progress")
|
||||
|
||||
//////////////////////
|
||||
// Embedded content //
|
||||
//////////////////////
|
||||
|
||||
// Vast majority not permitted
|
||||
// "audio" "canvas" "embed" "iframe" "object" "param" "source" "svg" "track"
|
||||
// "video" are all not permitted
|
||||
|
||||
p.AllowImages()
|
||||
|
||||
return p
|
||||
}
|
||||
203
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/policies_test.go
generated
vendored
203
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/policies_test.go
generated
vendored
@ -1,203 +0,0 @@
|
||||
// Copyright (c) 2014, David Kitchen <david@buro9.com>
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without
|
||||
// modification, are permitted provided that the following conditions are met:
|
||||
//
|
||||
// * Redistributions of source code must retain the above copyright notice, this
|
||||
// list of conditions and the following disclaimer.
|
||||
//
|
||||
// * Redistributions in binary form must reproduce the above copyright notice,
|
||||
// this list of conditions and the following disclaimer in the documentation
|
||||
// and/or other materials provided with the distribution.
|
||||
//
|
||||
// * Neither the name of the organisation (Microcosm) nor the names of its
|
||||
// contributors may be used to endorse or promote products derived from
|
||||
// this software without specific prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
|
||||
// AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
|
||||
// IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
|
||||
// DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
|
||||
// FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
|
||||
// DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
|
||||
// SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
|
||||
// CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
|
||||
// OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
|
||||
// OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
package bluemonday
|
||||
|
||||
import "testing"
|
||||
|
||||
func TestStrictPolicy(t *testing.T) {
|
||||
|
||||
p := StrictPolicy()
|
||||
|
||||
tests := []test{
|
||||
{
|
||||
in: "Hello, <b>World</b>!",
|
||||
expected: "Hello, World!",
|
||||
},
|
||||
{
|
||||
in: "<blockquote>Hello, <b>World</b>!",
|
||||
expected: "Hello, World!",
|
||||
},
|
||||
{ // Real world example from a message board
|
||||
in: `<quietly>email me - addy in profile</quiet>`,
|
||||
expected: `email me - addy in profile`,
|
||||
},
|
||||
{},
|
||||
}
|
||||
|
||||
for ii, test := range tests {
|
||||
out := p.Sanitize(test.in)
|
||||
if out != test.expected {
|
||||
t.Errorf(
|
||||
"test %d failed;\ninput : %s\noutput : %s\nexpected: %s",
|
||||
ii,
|
||||
test.in,
|
||||
out,
|
||||
test.expected,
|
||||
)
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
func TestUGCPolicy(t *testing.T) {
|
||||
|
||||
tests := []test{
|
||||
// Simple formatting
|
||||
{in: "Hello, World!", expected: "Hello, World!"},
|
||||
{in: "Hello, <b>World</b>!", expected: "Hello, <b>World</b>!"},
|
||||
// Blocks and formatting
|
||||
{
|
||||
in: "<p>Hello, <b onclick=alert(1337)>World</b>!</p>",
|
||||
expected: "<p>Hello, <b>World</b>!</p>",
|
||||
},
|
||||
{
|
||||
in: "<p onclick=alert(1337)>Hello, <b>World</b>!</p>",
|
||||
expected: "<p>Hello, <b>World</b>!</p>",
|
||||
},
|
||||
// Inline tags featuring globals
|
||||
{
|
||||
in: `<a href="http://example.org/" rel="nofollow">Hello, <b>World</b></a><a href="https://example.org/#!" rel="nofollow">!</a>`,
|
||||
expected: `<a href="http://example.org/" rel="nofollow">Hello, <b>World</b></a><a href="https://example.org/#%21" rel="nofollow">!</a>`,
|
||||
},
|
||||
{
|
||||
in: `Hello, <b>World</b><a title="!" href="https://example.org/#!" rel="nofollow">!</a>`,
|
||||
expected: `Hello, <b>World</b><a title="!" href="https://example.org/#%21" rel="nofollow">!</a>`,
|
||||
},
|
||||
// Images
|
||||
{
|
||||
in: `<a href="javascript:alert(1337)">foo</a>`,
|
||||
expected: `foo`,
|
||||
},
|
||||
{
|
||||
in: `<img src="http://example.org/foo.gif">`,
|
||||
expected: `<img src="http://example.org/foo.gif">`,
|
||||
},
|
||||
{
|
||||
in: `<img src="http://example.org/x.gif" alt="y" width=96 height=64 border=0>`,
|
||||
expected: `<img src="http://example.org/x.gif" alt="y" width="96" height="64">`,
|
||||
},
|
||||
{
|
||||
in: `<img src="http://example.org/x.png" alt="y" width="widgy" height=64 border=0>`,
|
||||
expected: `<img src="http://example.org/x.png" alt="y" height="64">`,
|
||||
},
|
||||
// Anchors
|
||||
{
|
||||
in: `<a href="foo.html">Link text</a>`,
|
||||
expected: `<a href="foo.html" rel="nofollow">Link text</a>`,
|
||||
},
|
||||
{
|
||||
in: `<a href="foo.html" onclick="alert(1337)">Link text</a>`,
|
||||
expected: `<a href="foo.html" rel="nofollow">Link text</a>`,
|
||||
},
|
||||
{
|
||||
in: `<a href="http://example.org/x.html" onclick="alert(1337)">Link text</a>`,
|
||||
expected: `<a href="http://example.org/x.html" rel="nofollow">Link text</a>`,
|
||||
},
|
||||
{
|
||||
in: `<a href="https://example.org/x.html" onclick="alert(1337)">Link text</a>`,
|
||||
expected: `<a href="https://example.org/x.html" rel="nofollow">Link text</a>`,
|
||||
},
|
||||
{
|
||||
in: `<a href="HTTPS://example.org/x.html" onclick="alert(1337)">Link text</a>`,
|
||||
expected: `<a href="https://example.org/x.html" rel="nofollow">Link text</a>`,
|
||||
},
|
||||
{
|
||||
in: `<a href="//example.org/x.html" onclick="alert(1337)">Link text</a>`,
|
||||
expected: `<a href="//example.org/x.html" rel="nofollow">Link text</a>`,
|
||||
},
|
||||
{
|
||||
in: `<a href="javascript:alert(1337).html" onclick="alert(1337)">Link text</a>`,
|
||||
expected: `Link text`,
|
||||
},
|
||||
{
|
||||
in: `<a name="header" id="header">Header text</a>`,
|
||||
expected: `<a id="header">Header text</a>`,
|
||||
},
|
||||
// Image map and links
|
||||
{
|
||||
in: `<img src="planets.gif" width="145" height="126" alt="" usemap="#demomap"><map name="demomap"><area shape="rect" coords="0,0,82,126" href="demo.htm" alt="1"><area shape="circle" coords="90,58,3" href="demo.htm" alt="2"><area shape="circle" coords="124,58,8" href="demo.htm" alt="3"></map>`,
|
||||
expected: `<img src="planets.gif" width="145" height="126" alt="" usemap="#demomap"><map name="demomap"><area shape="rect" coords="0,0,82,126" href="demo.htm" alt="1" rel="nofollow"><area shape="circle" coords="90,58,3" href="demo.htm" alt="2" rel="nofollow"><area shape="circle" coords="124,58,8" href="demo.htm" alt="3" rel="nofollow"></map>`,
|
||||
},
|
||||
// Tables
|
||||
{
|
||||
in: `<table style="color: rgb(0, 0, 0);">` +
|
||||
`<tbody>` +
|
||||
`<tr>` +
|
||||
`<th>Column One</th><th>Column Two</th>` +
|
||||
`</tr>` +
|
||||
`<tr>` +
|
||||
`<td align="center"` +
|
||||
` style="background-color: rgb(255, 255, 254);">` +
|
||||
`<font size="2">Size 2</font></td>` +
|
||||
`<td align="center"` +
|
||||
` style="background-color: rgb(255, 255, 254);">` +
|
||||
`<font size="7">Size 7</font></td>` +
|
||||
`</tr>` +
|
||||
`</tbody>` +
|
||||
`</table>`,
|
||||
expected: "" +
|
||||
`<table>` +
|
||||
`<tbody>` +
|
||||
`<tr>` +
|
||||
`<th>Column One</th><th>Column Two</th>` +
|
||||
`</tr>` +
|
||||
`<tr>` +
|
||||
`<td align="center">Size 2</td>` +
|
||||
`<td align="center">Size 7</td>` +
|
||||
`</tr>` +
|
||||
`</tbody>` +
|
||||
`</table>`,
|
||||
},
|
||||
// Ordering
|
||||
{
|
||||
in: `xss<a href="http://www.google.de" style="color:red;" onmouseover=alert(1) onmousemove="alert(2)" onclick=alert(3)>g<img src="http://example.org"/>oogle</a>`,
|
||||
expected: `xss<a href="http://www.google.de" rel="nofollow">g<img src="http://example.org"/>oogle</a>`,
|
||||
},
|
||||
// OWASP 25 June 2014 09:15 Strange behaviour
|
||||
{
|
||||
in: "<table>Hallo\r\n<script>SCRIPT</script>\nEnde\n\r",
|
||||
expected: "<table>Hallo\n\nEnde\n\n",
|
||||
},
|
||||
}
|
||||
|
||||
p := UGCPolicy()
|
||||
|
||||
for ii, test := range tests {
|
||||
out := p.Sanitize(test.in)
|
||||
if out != test.expected {
|
||||
t.Errorf(
|
||||
"test %d failed;\ninput : %s\noutput : %s\nexpected: %s",
|
||||
ii,
|
||||
test.in,
|
||||
out,
|
||||
test.expected,
|
||||
)
|
||||
}
|
||||
}
|
||||
}
|
||||
550
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/policy.go
generated
vendored
550
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/policy.go
generated
vendored
@ -1,550 +0,0 @@
|
||||
// Copyright (c) 2014, David Kitchen <david@buro9.com>
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without
|
||||
// modification, are permitted provided that the following conditions are met:
|
||||
//
|
||||
// * Redistributions of source code must retain the above copyright notice, this
|
||||
// list of conditions and the following disclaimer.
|
||||
//
|
||||
// * Redistributions in binary form must reproduce the above copyright notice,
|
||||
// this list of conditions and the following disclaimer in the documentation
|
||||
// and/or other materials provided with the distribution.
|
||||
//
|
||||
// * Neither the name of the organisation (Microcosm) nor the names of its
|
||||
// contributors may be used to endorse or promote products derived from
|
||||
// this software without specific prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
|
||||
// AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
|
||||
// IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
|
||||
// DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
|
||||
// FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
|
||||
// DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
|
||||
// SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
|
||||
// CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
|
||||
// OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
|
||||
// OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
package bluemonday
|
||||
|
||||
import (
|
||||
"net/url"
|
||||
"regexp"
|
||||
"strings"
|
||||
)
|
||||
|
||||
// Policy encapsulates the whitelist of HTML elements and attributes that will
|
||||
// be applied to the sanitised HTML.
|
||||
//
|
||||
// You should use bluemonday.NewPolicy() to create a blank policy as the
|
||||
// unexported fields contain maps that need to be initialized.
|
||||
type Policy struct {
|
||||
|
||||
// Declares whether the maps have been initialized, used as a cheap check to
|
||||
// ensure that those using Policy{} directly won't cause nil pointer
|
||||
// exceptions
|
||||
initialized bool
|
||||
|
||||
// Allows the <!DOCTYPE > tag to exist in the sanitized document
|
||||
allowDocType bool
|
||||
|
||||
// If true then we add spaces when stripping tags, specifically the closing
|
||||
// tag is replaced by a space character.
|
||||
addSpaces bool
|
||||
|
||||
// When true, add rel="nofollow" to HTML anchors
|
||||
requireNoFollow bool
|
||||
|
||||
// When true, add rel="nofollow" to HTML anchors
|
||||
// Will add for href="http://foo"
|
||||
// Will skip for href="/foo" or href="foo"
|
||||
requireNoFollowFullyQualifiedLinks bool
|
||||
|
||||
// When true add target="_blank" to fully qualified links
|
||||
// Will add for href="http://foo"
|
||||
// Will skip for href="/foo" or href="foo"
|
||||
addTargetBlankToFullyQualifiedLinks bool
|
||||
|
||||
// When true, URLs must be parseable by "net/url" url.Parse()
|
||||
requireParseableURLs bool
|
||||
|
||||
// When true, u, _ := url.Parse("url"); !u.IsAbs() is permitted
|
||||
allowRelativeURLs bool
|
||||
|
||||
// map[htmlElementName]map[htmlAttributeName]attrPolicy
|
||||
elsAndAttrs map[string]map[string]attrPolicy
|
||||
|
||||
// map[htmlAttributeName]attrPolicy
|
||||
globalAttrs map[string]attrPolicy
|
||||
|
||||
// If urlPolicy is nil, all URLs with matching schema are allowed.
|
||||
// Otherwise, only the URLs with matching schema and urlPolicy(url)
|
||||
// returning true are allowed.
|
||||
allowURLSchemes map[string]urlPolicy
|
||||
|
||||
// If an element has had all attributes removed as a result of a policy
|
||||
// being applied, then the element would be removed from the output.
|
||||
//
|
||||
// However some elements are valid and have strong layout meaning without
|
||||
// any attributes, i.e. <table>. To prevent those being removed we maintain
|
||||
// a list of elements that are allowed to have no attributes and that will
|
||||
// be maintained in the output HTML.
|
||||
setOfElementsAllowedWithoutAttrs map[string]struct{}
|
||||
|
||||
setOfElementsToSkipContent map[string]struct{}
|
||||
}
|
||||
|
||||
type attrPolicy struct {
|
||||
|
||||
// optional pattern to match, when not nil the regexp needs to match
|
||||
// otherwise the attribute is removed
|
||||
regexp *regexp.Regexp
|
||||
}
|
||||
|
||||
type attrPolicyBuilder struct {
|
||||
p *Policy
|
||||
|
||||
attrNames []string
|
||||
regexp *regexp.Regexp
|
||||
allowEmpty bool
|
||||
}
|
||||
|
||||
type urlPolicy func(url *url.URL) (allowUrl bool)
|
||||
|
||||
// init initializes the maps if this has not been done already
|
||||
func (p *Policy) init() {
|
||||
if !p.initialized {
|
||||
p.elsAndAttrs = make(map[string]map[string]attrPolicy)
|
||||
p.globalAttrs = make(map[string]attrPolicy)
|
||||
p.allowURLSchemes = make(map[string]urlPolicy)
|
||||
p.setOfElementsAllowedWithoutAttrs = make(map[string]struct{})
|
||||
p.setOfElementsToSkipContent = make(map[string]struct{})
|
||||
p.initialized = true
|
||||
}
|
||||
}
|
||||
|
||||
// NewPolicy returns a blank policy with nothing whitelisted or permitted. This
|
||||
// is the recommended way to start building a policy and you should now use
|
||||
// AllowAttrs() and/or AllowElements() to construct the whitelist of HTML
|
||||
// elements and attributes.
|
||||
func NewPolicy() *Policy {
|
||||
|
||||
p := Policy{}
|
||||
|
||||
p.addDefaultElementsWithoutAttrs()
|
||||
p.addDefaultSkipElementContent()
|
||||
|
||||
return &p
|
||||
}
|
||||
|
||||
// AllowAttrs takes a range of HTML attribute names and returns an
|
||||
// attribute policy builder that allows you to specify the pattern and scope of
|
||||
// the whitelisted attribute.
|
||||
//
|
||||
// The attribute policy is only added to the core policy when either Globally()
|
||||
// or OnElements(...) are called.
|
||||
func (p *Policy) AllowAttrs(attrNames ...string) *attrPolicyBuilder {
|
||||
|
||||
p.init()
|
||||
|
||||
abp := attrPolicyBuilder{
|
||||
p: p,
|
||||
allowEmpty: false,
|
||||
}
|
||||
|
||||
for _, attrName := range attrNames {
|
||||
abp.attrNames = append(abp.attrNames, strings.ToLower(attrName))
|
||||
}
|
||||
|
||||
return &abp
|
||||
}
|
||||
|
||||
// AllowNoAttrs says that attributes on element are optional.
|
||||
//
|
||||
// The attribute policy is only added to the core policy when OnElements(...)
|
||||
// are called.
|
||||
func (p *Policy) AllowNoAttrs() *attrPolicyBuilder {
|
||||
|
||||
p.init()
|
||||
|
||||
abp := attrPolicyBuilder{
|
||||
p: p,
|
||||
allowEmpty: true,
|
||||
}
|
||||
return &abp
|
||||
}
|
||||
|
||||
// AllowNoAttrs says that attributes on element are optional.
|
||||
//
|
||||
// The attribute policy is only added to the core policy when OnElements(...)
|
||||
// are called.
|
||||
func (abp *attrPolicyBuilder) AllowNoAttrs() *attrPolicyBuilder {
|
||||
|
||||
abp.allowEmpty = true
|
||||
|
||||
return abp
|
||||
}
|
||||
|
||||
// Matching allows a regular expression to be applied to a nascent attribute
|
||||
// policy, and returns the attribute policy. Calling this more than once will
|
||||
// replace the existing regexp.
|
||||
func (abp *attrPolicyBuilder) Matching(regex *regexp.Regexp) *attrPolicyBuilder {
|
||||
|
||||
abp.regexp = regex
|
||||
|
||||
return abp
|
||||
}
|
||||
|
||||
// OnElements will bind an attribute policy to a given range of HTML elements
|
||||
// and return the updated policy
|
||||
func (abp *attrPolicyBuilder) OnElements(elements ...string) *Policy {
|
||||
|
||||
for _, element := range elements {
|
||||
element = strings.ToLower(element)
|
||||
|
||||
for _, attr := range abp.attrNames {
|
||||
|
||||
if _, ok := abp.p.elsAndAttrs[element]; !ok {
|
||||
abp.p.elsAndAttrs[element] = make(map[string]attrPolicy)
|
||||
}
|
||||
|
||||
ap := attrPolicy{}
|
||||
if abp.regexp != nil {
|
||||
ap.regexp = abp.regexp
|
||||
}
|
||||
|
||||
abp.p.elsAndAttrs[element][attr] = ap
|
||||
}
|
||||
|
||||
if abp.allowEmpty {
|
||||
abp.p.setOfElementsAllowedWithoutAttrs[element] = struct{}{}
|
||||
|
||||
if _, ok := abp.p.elsAndAttrs[element]; !ok {
|
||||
abp.p.elsAndAttrs[element] = make(map[string]attrPolicy)
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
return abp.p
|
||||
}
|
||||
|
||||
// Globally will bind an attribute policy to all HTML elements and return the
|
||||
// updated policy
|
||||
func (abp *attrPolicyBuilder) Globally() *Policy {
|
||||
|
||||
for _, attr := range abp.attrNames {
|
||||
if _, ok := abp.p.globalAttrs[attr]; !ok {
|
||||
abp.p.globalAttrs[attr] = attrPolicy{}
|
||||
}
|
||||
|
||||
ap := attrPolicy{}
|
||||
if abp.regexp != nil {
|
||||
ap.regexp = abp.regexp
|
||||
}
|
||||
|
||||
abp.p.globalAttrs[attr] = ap
|
||||
}
|
||||
|
||||
return abp.p
|
||||
}
|
||||
|
||||
// AllowElements will append HTML elements to the whitelist without applying an
|
||||
// attribute policy to those elements (the elements are permitted
|
||||
// sans-attributes)
|
||||
func (p *Policy) AllowElements(names ...string) *Policy {
|
||||
p.init()
|
||||
|
||||
for _, element := range names {
|
||||
element = strings.ToLower(element)
|
||||
|
||||
if _, ok := p.elsAndAttrs[element]; !ok {
|
||||
p.elsAndAttrs[element] = make(map[string]attrPolicy)
|
||||
}
|
||||
}
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// RequireNoFollowOnLinks will result in all <a> tags having a rel="nofollow"
|
||||
// added to them if one does not already exist
|
||||
//
|
||||
// Note: This requires p.RequireParseableURLs(true) and will enable it.
|
||||
func (p *Policy) RequireNoFollowOnLinks(require bool) *Policy {
|
||||
|
||||
p.requireNoFollow = require
|
||||
p.requireParseableURLs = true
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// RequireNoFollowOnFullyQualifiedLinks will result in all <a> tags that point
|
||||
// to a non-local destination (i.e. starts with a protocol and has a host)
|
||||
// having a rel="nofollow" added to them if one does not already exist
|
||||
//
|
||||
// Note: This requires p.RequireParseableURLs(true) and will enable it.
|
||||
func (p *Policy) RequireNoFollowOnFullyQualifiedLinks(require bool) *Policy {
|
||||
|
||||
p.requireNoFollowFullyQualifiedLinks = require
|
||||
p.requireParseableURLs = true
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// AddTargetBlankToFullyQualifiedLinks will result in all <a> tags that point
|
||||
// to a non-local destination (i.e. starts with a protocol and has a host)
|
||||
// having a target="_blank" added to them if one does not already exist
|
||||
//
|
||||
// Note: This requires p.RequireParseableURLs(true) and will enable it.
|
||||
func (p *Policy) AddTargetBlankToFullyQualifiedLinks(require bool) *Policy {
|
||||
|
||||
p.addTargetBlankToFullyQualifiedLinks = require
|
||||
p.requireParseableURLs = true
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// RequireParseableURLs will result in all URLs requiring that they be parseable
|
||||
// by "net/url" url.Parse()
|
||||
// This applies to:
|
||||
// - a.href
|
||||
// - area.href
|
||||
// - blockquote.cite
|
||||
// - img.src
|
||||
// - link.href
|
||||
// - script.src
|
||||
func (p *Policy) RequireParseableURLs(require bool) *Policy {
|
||||
|
||||
p.requireParseableURLs = require
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// AllowRelativeURLs enables RequireParseableURLs and then permits URLs that
|
||||
// are parseable, have no schema information and url.IsAbs() returns false
|
||||
// This permits local URLs
|
||||
func (p *Policy) AllowRelativeURLs(require bool) *Policy {
|
||||
|
||||
p.RequireParseableURLs(true)
|
||||
p.allowRelativeURLs = require
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// AllowURLSchemes will append URL schemes to the whitelist
|
||||
// Example: p.AllowURLSchemes("mailto", "http", "https")
|
||||
func (p *Policy) AllowURLSchemes(schemes ...string) *Policy {
|
||||
p.init()
|
||||
|
||||
p.RequireParseableURLs(true)
|
||||
|
||||
for _, scheme := range schemes {
|
||||
scheme = strings.ToLower(scheme)
|
||||
|
||||
// Allow all URLs with matching scheme.
|
||||
p.allowURLSchemes[scheme] = nil
|
||||
}
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// AllowURLSchemeWithCustomPolicy will append URL schemes with
|
||||
// a custom URL policy to the whitelist.
|
||||
// Only the URLs with matching schema and urlPolicy(url)
|
||||
// returning true will be allowed.
|
||||
func (p *Policy) AllowURLSchemeWithCustomPolicy(
|
||||
scheme string,
|
||||
urlPolicy func(url *url.URL) (allowUrl bool),
|
||||
) *Policy {
|
||||
|
||||
p.init()
|
||||
|
||||
p.RequireParseableURLs(true)
|
||||
|
||||
scheme = strings.ToLower(scheme)
|
||||
|
||||
p.allowURLSchemes[scheme] = urlPolicy
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// AllowDocType states whether the HTML sanitised by the sanitizer is allowed to
|
||||
// contain the HTML DocType tag: <!DOCTYPE HTML> or one of it's variants.
|
||||
//
|
||||
// The HTML spec only permits one doctype per document, and as you know how you
|
||||
// are using the output of this, you know best as to whether we should ignore it
|
||||
// (default) or not.
|
||||
//
|
||||
// If you are sanitizing a HTML fragment the default (false) is fine.
|
||||
func (p *Policy) AllowDocType(allow bool) *Policy {
|
||||
|
||||
p.allowDocType = allow
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// AddSpaceWhenStrippingTag states whether to add a single space " " when
|
||||
// removing tags that are not whitelisted by the policy.
|
||||
//
|
||||
// This is useful if you expect to strip tags in dense markup and may lose the
|
||||
// value of whitespace.
|
||||
//
|
||||
// For example: "<p>Hello</p><p>World</p>"" would be sanitized to "HelloWorld"
|
||||
// with the default value of false, but you may wish to sanitize this to
|
||||
// " Hello World " by setting AddSpaceWhenStrippingTag to true as this would
|
||||
// retain the intent of the text.
|
||||
func (p *Policy) AddSpaceWhenStrippingTag(allow bool) *Policy {
|
||||
|
||||
p.addSpaces = allow
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// SkipElementsContent adds the HTML elements whose tags is needed to be removed
|
||||
// with it's content.
|
||||
func (p *Policy) SkipElementsContent(names ...string) *Policy {
|
||||
|
||||
p.init()
|
||||
|
||||
for _, element := range names {
|
||||
element = strings.ToLower(element)
|
||||
|
||||
if _, ok := p.setOfElementsToSkipContent[element]; !ok {
|
||||
p.setOfElementsToSkipContent[element] = struct{}{}
|
||||
}
|
||||
}
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// AllowElementsContent marks the HTML elements whose content should be
|
||||
// retained after removing the tag.
|
||||
func (p *Policy) AllowElementsContent(names ...string) *Policy {
|
||||
|
||||
p.init()
|
||||
|
||||
for _, element := range names {
|
||||
delete(p.setOfElementsToSkipContent, strings.ToLower(element))
|
||||
}
|
||||
|
||||
return p
|
||||
}
|
||||
|
||||
// addDefaultElementsWithoutAttrs adds the HTML elements that we know are valid
|
||||
// without any attributes to an internal map.
|
||||
// i.e. we know that <table> is valid, but <bdo> isn't valid as the "dir" attr
|
||||
// is mandatory
|
||||
func (p *Policy) addDefaultElementsWithoutAttrs() {
|
||||
p.init()
|
||||
|
||||
p.setOfElementsAllowedWithoutAttrs["abbr"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["acronym"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["article"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["aside"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["audio"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["b"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["bdi"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["blockquote"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["body"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["br"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["button"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["canvas"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["caption"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["center"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["cite"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["code"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["col"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["colgroup"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["datalist"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["dd"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["del"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["details"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["dfn"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["div"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["dl"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["dt"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["em"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["fieldset"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["figcaption"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["figure"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["footer"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["h1"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["h2"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["h3"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["h4"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["h5"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["h6"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["head"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["header"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["hgroup"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["hr"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["html"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["i"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["ins"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["kbd"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["li"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["mark"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["marquee"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["nav"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["ol"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["optgroup"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["option"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["p"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["pre"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["q"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["rp"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["rt"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["ruby"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["s"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["samp"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["section"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["select"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["small"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["span"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["strike"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["strong"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["style"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["sub"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["summary"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["sup"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["svg"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["table"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["tbody"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["td"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["textarea"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["tfoot"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["th"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["thead"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["title"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["time"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["tr"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["tt"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["u"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["ul"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["var"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["video"] = struct{}{}
|
||||
p.setOfElementsAllowedWithoutAttrs["wbr"] = struct{}{}
|
||||
|
||||
}
|
||||
|
||||
// addDefaultSkipElementContent adds the HTML elements that we should skip
|
||||
// rendering the character content of, if the element itself is not allowed.
|
||||
// This is all character data that the end user would not normally see.
|
||||
// i.e. if we exclude a <script> tag then we shouldn't render the JavaScript or
|
||||
// anything else until we encounter the closing </script> tag.
|
||||
func (p *Policy) addDefaultSkipElementContent() {
|
||||
p.init()
|
||||
|
||||
p.setOfElementsToSkipContent["frame"] = struct{}{}
|
||||
p.setOfElementsToSkipContent["frameset"] = struct{}{}
|
||||
p.setOfElementsToSkipContent["iframe"] = struct{}{}
|
||||
p.setOfElementsToSkipContent["noembed"] = struct{}{}
|
||||
p.setOfElementsToSkipContent["noframes"] = struct{}{}
|
||||
p.setOfElementsToSkipContent["noscript"] = struct{}{}
|
||||
p.setOfElementsToSkipContent["nostyle"] = struct{}{}
|
||||
p.setOfElementsToSkipContent["object"] = struct{}{}
|
||||
p.setOfElementsToSkipContent["script"] = struct{}{}
|
||||
p.setOfElementsToSkipContent["style"] = struct{}{}
|
||||
p.setOfElementsToSkipContent["title"] = struct{}{}
|
||||
}
|
||||
60
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/policy_test.go
generated
vendored
60
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/policy_test.go
generated
vendored
@ -1,60 +0,0 @@
|
||||
// Copyright (c) 2014, David Kitchen <david@buro9.com>
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without
|
||||
// modification, are permitted provided that the following conditions are met:
|
||||
//
|
||||
// * Redistributions of source code must retain the above copyright notice, this
|
||||
// list of conditions and the following disclaimer.
|
||||
//
|
||||
// * Redistributions in binary form must reproduce the above copyright notice,
|
||||
// this list of conditions and the following disclaimer in the documentation
|
||||
// and/or other materials provided with the distribution.
|
||||
//
|
||||
// * Neither the name of the organisation (Microcosm) nor the names of its
|
||||
// contributors may be used to endorse or promote products derived from
|
||||
// this software without specific prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
|
||||
// AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
|
||||
// IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
|
||||
// DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
|
||||
// FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
|
||||
// DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
|
||||
// SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
|
||||
// CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
|
||||
// OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
|
||||
// OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
package bluemonday
|
||||
|
||||
import "testing"
|
||||
|
||||
func TestAllowElementsContent(t *testing.T) {
|
||||
policy := NewPolicy().AllowElementsContent("iframe", "script")
|
||||
|
||||
tests := []test{
|
||||
{
|
||||
in: "<iframe src='http://url.com/test'>this is fallback content</iframe>",
|
||||
expected: "this is fallback content",
|
||||
},
|
||||
{
|
||||
in: "<script>var a = 10; alert(a);</script>",
|
||||
expected: "var a = 10; alert(a);",
|
||||
},
|
||||
}
|
||||
|
||||
for ii, test := range tests {
|
||||
out := policy.Sanitize(test.in)
|
||||
if out != test.expected {
|
||||
t.Errorf(
|
||||
"test %d failed;\ninput : %s\noutput : %s\nexpected: %s",
|
||||
ii,
|
||||
test.in,
|
||||
out,
|
||||
test.expected,
|
||||
)
|
||||
}
|
||||
}
|
||||
}
|
||||
539
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/sanitize.go
generated
vendored
539
sample-functions/MarkdownRender/vendor/github.com/microcosm-cc/bluemonday/sanitize.go
generated
vendored
@ -1,539 +0,0 @@
|
||||
// Copyright (c) 2014, David Kitchen <david@buro9.com>
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without
|
||||
// modification, are permitted provided that the following conditions are met:
|
||||
//
|
||||
// * Redistributions of source code must retain the above copyright notice, this
|
||||
// list of conditions and the following disclaimer.
|
||||
//
|
||||
// * Redistributions in binary form must reproduce the above copyright notice,
|
||||
// this list of conditions and the following disclaimer in the documentation
|
||||
// and/or other materials provided with the distribution.
|
||||
//
|
||||
// * Neither the name of the organisation (Microcosm) nor the names of its
|
||||
// contributors may be used to endorse or promote products derived from
|
||||
// this software without specific prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
|
||||
// AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
|
||||
// IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
|
||||
// DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
|
||||
// FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
|
||||
// DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
|
||||
// SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
|
||||
// CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
|
||||
// OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
|
||||
// OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
package bluemonday
|
||||
|
||||
import (
|
||||
"bytes"
|
||||
"io"
|
||||
"net/url"
|
||||
"strings"
|
||||
|
||||
"golang.org/x/net/html"
|
||||
)
|
||||
|
||||
// Sanitize takes a string that contains a HTML fragment or document and applies
|
||||
// the given policy whitelist.
|
||||
//
|
||||
// It returns a HTML string that has been sanitized by the policy or an empty
|
||||
// string if an error has occurred (most likely as a consequence of extremely
|
||||
// malformed input)
|
||||
func (p *Policy) Sanitize(s string) string {
|
||||
if strings.TrimSpace(s) == "" {
|
||||
return s
|
||||
}
|
||||
|
||||
return p.sanitize(strings.NewReader(s)).String()
|
||||
}
|
||||
|
||||
// SanitizeBytes takes a []byte that contains a HTML fragment or document and applies
|
||||
// the given policy whitelist.
|
||||
//
|
||||
// It returns a []byte containing the HTML that has been sanitized by the policy
|
||||
// or an empty []byte if an error has occurred (most likely as a consequence of
|
||||
// extremely malformed input)
|
||||
func (p *Policy) SanitizeBytes(b []byte) []byte {
|
||||
if len(bytes.TrimSpace(b)) == 0 {
|
||||
return b
|
||||
}
|
||||
|
||||
return p.sanitize(bytes.NewReader(b)).Bytes()
|
||||
}
|
||||
|
||||
// SanitizeReader takes an io.Reader that contains a HTML fragment or document
|
||||
// and applies the given policy whitelist.
|
||||
//
|
||||
// It returns a bytes.Buffer containing the HTML that has been sanitized by the
|
||||
// policy. Errors during sanitization will merely return an empty result.
|
||||
func (p *Policy) SanitizeReader(r io.Reader) *bytes.Buffer {
|
||||
return p.sanitize(r)
|
||||
}
|
||||
|
||||
// Performs the actual sanitization process.
|
||||
func (p *Policy) sanitize(r io.Reader) *bytes.Buffer {
|
||||
|
||||
// It is possible that the developer has created the policy via:
|
||||
// p := bluemonday.Policy{}
|
||||
// rather than:
|
||||
// p := bluemonday.NewPolicy()
|
||||
// If this is the case, and if they haven't yet triggered an action that
|
||||
// would initiliaze the maps, then we need to do that.
|
||||
p.init()
|
||||
|
||||
var (
|
||||
buff bytes.Buffer
|
||||
skipElementContent bool
|
||||
skippingElementsCount int64
|
||||
skipClosingTag bool
|
||||
closingTagToSkipStack []string
|
||||
mostRecentlyStartedToken string
|
||||
)
|
||||
|
||||
tokenizer := html.NewTokenizer(r)
|
||||
for {
|
||||
if tokenizer.Next() == html.ErrorToken {
|
||||
err := tokenizer.Err()
|
||||
if err == io.EOF {
|
||||
// End of input means end of processing
|
||||
return &buff
|
||||
}
|
||||
|
||||
// Raw tokenizer error
|
||||
return &bytes.Buffer{}
|
||||
}
|
||||
|
||||
token := tokenizer.Token()
|
||||
switch token.Type {
|
||||
case html.DoctypeToken:
|
||||
|
||||
if p.allowDocType {
|
||||
buff.WriteString(token.String())
|
||||
}
|
||||
|
||||
case html.CommentToken:
|
||||
|
||||
// Comments are ignored by default
|
||||
|
||||
case html.StartTagToken:
|
||||
|
||||
mostRecentlyStartedToken = token.Data
|
||||
|
||||
aps, ok := p.elsAndAttrs[token.Data]
|
||||
if !ok {
|
||||
if _, ok := p.setOfElementsToSkipContent[token.Data]; ok {
|
||||
skipElementContent = true
|
||||
skippingElementsCount++
|
||||
}
|
||||
if p.addSpaces {
|
||||
buff.WriteString(" ")
|
||||
}
|
||||
break
|
||||
}
|
||||
|
||||
if len(token.Attr) != 0 {
|
||||
token.Attr = p.sanitizeAttrs(token.Data, token.Attr, aps)
|
||||
}
|
||||
|
||||
if len(token.Attr) == 0 {
|
||||
if !p.allowNoAttrs(token.Data) {
|
||||
skipClosingTag = true
|
||||
closingTagToSkipStack = append(closingTagToSkipStack, token.Data)
|
||||
if p.addSpaces {
|
||||
buff.WriteString(" ")
|
||||
}
|
||||
break
|
||||
}
|
||||
}
|
||||
|
||||
if !skipElementContent {
|
||||
buff.WriteString(token.String())
|
||||
}
|
||||
|
||||
case html.EndTagToken:
|
||||
|
||||
if mostRecentlyStartedToken == token.Data {
|
||||
mostRecentlyStartedToken = ""
|
||||
}
|
||||
|
||||
if skipClosingTag && closingTagToSkipStack[len(closingTagToSkipStack)-1] == token.Data {
|
||||
closingTagToSkipStack = closingTagToSkipStack[:len(closingTagToSkipStack)-1]
|
||||
if len(closingTagToSkipStack) == 0 {
|
||||
skipClosingTag = false
|
||||
}
|
||||
if p.addSpaces {
|
||||
buff.WriteString(" ")
|
||||
}
|
||||
break
|
||||
}
|
||||
|
||||
if _, ok := p.elsAndAttrs[token.Data]; !ok {
|
||||
if _, ok := p.setOfElementsToSkipContent[token.Data]; ok {
|
||||
skippingElementsCount--
|
||||
if skippingElementsCount == 0 {
|
||||
skipElementContent = false
|
||||
}
|
||||
}
|
||||
if p.addSpaces {
|
||||
buff.WriteString(" ")
|
||||
}
|
||||
break
|
||||
}
|
||||
|
||||
if !skipElementContent {
|
||||
buff.WriteString(token.String())
|
||||
}
|
||||
|
||||
case html.SelfClosingTagToken:
|
||||
|
||||
aps, ok := p.elsAndAttrs[token.Data]
|
||||
if !ok {
|
||||
if p.addSpaces {
|
||||
buff.WriteString(" ")
|
||||
}
|
||||
break
|
||||
}
|
||||
|
||||
if len(token.Attr) != 0 {
|
||||
token.Attr = p.sanitizeAttrs(token.Data, token.Attr, aps)
|
||||
}
|
||||
|
||||
if len(token.Attr) == 0 && !p.allowNoAttrs(token.Data) {
|
||||
if p.addSpaces {
|
||||
buff.WriteString(" ")
|
||||
}
|
||||
break
|
||||
}
|
||||
|
||||
if !skipElementContent {
|
||||
buff.WriteString(token.String())
|
||||
}
|
||||
|
||||
case html.TextToken:
|
||||
|
||||
if !skipElementContent {
|
||||
switch strings.ToLower(mostRecentlyStartedToken) {
|
||||
case "script":
|
||||
// not encouraged, but if a policy allows JavaScript we
|
||||
// should not HTML escape it as that would break the output
|
||||
buff.WriteString(token.Data)
|
||||
case "style":
|
||||
// not encouraged, but if a policy allows CSS styles we
|
||||
// should not HTML escape it as that would break the output
|
||||
buff.WriteString(token.Data)
|
||||
default:
|
||||
// HTML escape the text
|
||||
buff.WriteString(token.String())
|
||||
}
|
||||
}
|
||||
|
||||
default:
|
||||
// A token that didn't exist in the html package when we wrote this
|
||||
return &bytes.Buffer{}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
// sanitizeAttrs takes a set of element attribute policies and the global
|
||||
// attribute policies and applies them to the []html.Attribute returning a set
|
||||
// of html.Attributes that match the policies
|
||||
func (p *Policy) sanitizeAttrs(
|
||||
elementName string,
|
||||
attrs []html.Attribute,
|
||||
aps map[string]attrPolicy,
|
||||
) []html.Attribute {
|
||||
|
||||
if len(attrs) == 0 {
|
||||
return attrs
|
||||
}
|
||||
|
||||
// Builds a new attribute slice based on the whether the attribute has been
|
||||
// whitelisted explicitly or globally.
|
||||
cleanAttrs := []html.Attribute{}
|
||||
for _, htmlAttr := range attrs {
|
||||
// Is there an element specific attribute policy that applies?
|
||||
if ap, ok := aps[htmlAttr.Key]; ok {
|
||||
if ap.regexp != nil {
|
||||
if ap.regexp.MatchString(htmlAttr.Val) {
|
||||
cleanAttrs = append(cleanAttrs, htmlAttr)
|
||||
continue
|
||||
}
|
||||
} else {
|
||||
cleanAttrs = append(cleanAttrs, htmlAttr)
|
||||
continue
|
||||
}
|
||||
}
|
||||
|
||||
// Is there a global attribute policy that applies?
|
||||
if ap, ok := p.globalAttrs[htmlAttr.Key]; ok {
|
||||
if ap.regexp != nil {
|
||||
if ap.regexp.MatchString(htmlAttr.Val) {
|
||||
cleanAttrs = append(cleanAttrs, htmlAttr)
|
||||
}
|
||||
} else {
|
||||
cleanAttrs = append(cleanAttrs, htmlAttr)
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
if len(cleanAttrs) == 0 {
|
||||
// If nothing was allowed, let's get out of here
|
||||
return cleanAttrs
|
||||
}
|
||||
// cleanAttrs now contains the attributes that are permitted
|
||||
|
||||
if linkable(elementName) {
|
||||
if p.requireParseableURLs {
|
||||
// Ensure URLs are parseable:
|
||||
// - a.href
|
||||
// - area.href
|
||||
// - link.href
|
||||
// - blockquote.cite
|
||||
// - q.cite
|
||||
// - img.src
|
||||
// - script.src
|
||||
tmpAttrs := []html.Attribute{}
|
||||
for _, htmlAttr := range cleanAttrs {
|
||||
switch elementName {
|
||||
case "a", "area", "link":
|
||||
if htmlAttr.Key == "href" {
|
||||
if u, ok := p.validURL(htmlAttr.Val); ok {
|
||||
htmlAttr.Val = u
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
}
|
||||
break
|
||||
}
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
case "blockquote", "q":
|
||||
if htmlAttr.Key == "cite" {
|
||||
if u, ok := p.validURL(htmlAttr.Val); ok {
|
||||
htmlAttr.Val = u
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
}
|
||||
break
|
||||
}
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
case "img", "script":
|
||||
if htmlAttr.Key == "src" {
|
||||
if u, ok := p.validURL(htmlAttr.Val); ok {
|
||||
htmlAttr.Val = u
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
}
|
||||
break
|
||||
}
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
default:
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
}
|
||||
}
|
||||
cleanAttrs = tmpAttrs
|
||||
}
|
||||
|
||||
if (p.requireNoFollow ||
|
||||
p.requireNoFollowFullyQualifiedLinks ||
|
||||
p.addTargetBlankToFullyQualifiedLinks) &&
|
||||
len(cleanAttrs) > 0 {
|
||||
|
||||
// Add rel="nofollow" if a "href" exists
|
||||
switch elementName {
|
||||
case "a", "area", "link":
|
||||
var hrefFound bool
|
||||
var externalLink bool
|
||||
for _, htmlAttr := range cleanAttrs {
|
||||
if htmlAttr.Key == "href" {
|
||||
hrefFound = true
|
||||
|
||||
u, err := url.Parse(htmlAttr.Val)
|
||||
if err != nil {
|
||||
continue
|
||||
}
|
||||
if u.Host != "" {
|
||||
externalLink = true
|
||||
}
|
||||
|
||||
continue
|
||||
}
|
||||
}
|
||||
|
||||
if hrefFound {
|
||||
var (
|
||||
noFollowFound bool
|
||||
targetBlankFound bool
|
||||
)
|
||||
|
||||
addNoFollow := (p.requireNoFollow ||
|
||||
externalLink && p.requireNoFollowFullyQualifiedLinks)
|
||||
|
||||
addTargetBlank := (externalLink &&
|
||||
p.addTargetBlankToFullyQualifiedLinks)
|
||||
|
||||
tmpAttrs := []html.Attribute{}
|
||||
for _, htmlAttr := range cleanAttrs {
|
||||
|
||||
var appended bool
|
||||
if htmlAttr.Key == "rel" && addNoFollow {
|
||||
|
||||
if strings.Contains(htmlAttr.Val, "nofollow") {
|
||||
noFollowFound = true
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
appended = true
|
||||
} else {
|
||||
htmlAttr.Val += " nofollow"
|
||||
noFollowFound = true
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
appended = true
|
||||
}
|
||||
}
|
||||
|
||||
if elementName == "a" && htmlAttr.Key == "target" {
|
||||
if htmlAttr.Val == "_blank" {
|
||||
targetBlankFound = true
|
||||
}
|
||||
if addTargetBlank && !targetBlankFound {
|
||||
htmlAttr.Val = "_blank"
|
||||
targetBlankFound = true
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
appended = true
|
||||
}
|
||||
}
|
||||
|
||||
if !appended {
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
}
|
||||
}
|
||||
if noFollowFound || targetBlankFound {
|
||||
cleanAttrs = tmpAttrs
|
||||
}
|
||||
|
||||
if addNoFollow && !noFollowFound {
|
||||
rel := html.Attribute{}
|
||||
rel.Key = "rel"
|
||||
rel.Val = "nofollow"
|
||||
cleanAttrs = append(cleanAttrs, rel)
|
||||
}
|
||||
|
||||
if elementName == "a" && addTargetBlank && !targetBlankFound {
|
||||
rel := html.Attribute{}
|
||||
rel.Key = "target"
|
||||
rel.Val = "_blank"
|
||||
targetBlankFound = true
|
||||
cleanAttrs = append(cleanAttrs, rel)
|
||||
}
|
||||
|
||||
if targetBlankFound {
|
||||
// target="_blank" has a security risk that allows the
|
||||
// opened window/tab to issue JavaScript calls against
|
||||
// window.opener, which in effect allow the destination
|
||||
// of the link to control the source:
|
||||
// https://dev.to/ben/the-targetblank-vulnerability-by-example
|
||||
//
|
||||
// To mitigate this risk, we need to add a specific rel
|
||||
// attribute if it is not already present.
|
||||
// rel="noopener"
|
||||
//
|
||||
// Unfortunately this is processing the rel twice (we
|
||||
// already looked at it earlier ^^) as we cannot be sure
|
||||
// of the ordering of the href and rel, and whether we
|
||||
// have fully satisfied that we need to do this. This
|
||||
// double processing only happens *if* target="_blank"
|
||||
// is true.
|
||||
var noOpenerAdded bool
|
||||
tmpAttrs := []html.Attribute{}
|
||||
for _, htmlAttr := range cleanAttrs {
|
||||
var appended bool
|
||||
if htmlAttr.Key == "rel" {
|
||||
if strings.Contains(htmlAttr.Val, "noopener") {
|
||||
noOpenerAdded = true
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
} else {
|
||||
htmlAttr.Val += " noopener"
|
||||
noOpenerAdded = true
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
}
|
||||
|
||||
appended = true
|
||||
}
|
||||
if !appended {
|
||||
tmpAttrs = append(tmpAttrs, htmlAttr)
|
||||
}
|
||||
}
|
||||
if noOpenerAdded {
|
||||
cleanAttrs = tmpAttrs
|
||||
} else {
|
||||
// rel attr was not found, or else noopener would
|
||||
// have been added already
|
||||
rel := html.Attribute{}
|
||||
rel.Key = "rel"
|
||||
rel.Val = "noopener"
|
||||
cleanAttrs = append(cleanAttrs, rel)
|
||||
}
|
||||
|
||||
}
|
||||
}
|
||||
default:
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
return cleanAttrs
|
||||
}
|
||||
|
||||
func (p *Policy) allowNoAttrs(elementName string) bool {
|
||||
_, ok := p.setOfElementsAllowedWithoutAttrs[elementName]
|
||||
return ok
|
||||
}
|
||||
|
||||
func (p *Policy) validURL(rawurl string) (string, bool) {
|
||||
if p.requireParseableURLs {
|
||||
// URLs do not contain whitespace
|
||||
if strings.Contains(rawurl, " ") ||
|
||||
strings.Contains(rawurl, "\t") ||
|
||||
strings.Contains(rawurl, "\n") {
|
||||
return "", false
|
||||
}
|
||||
|
||||
u, err := url.Parse(rawurl)
|
||||
if err != nil {
|
||||
return "", false
|
||||
}
|
||||
|
||||
if u.Scheme != "" {
|
||||
|
||||
urlPolicy, ok := p.allowURLSchemes[u.Scheme]
|
||||
if !ok {
|
||||
return "", false
|
||||
|
||||
}
|
||||
|
||||
if urlPolicy == nil || urlPolicy(u) == true {
|
||||
return u.String(), true
|
||||
}
|
||||
|
||||
return "", false
|
||||
}
|
||||
|
||||
if p.allowRelativeURLs {
|
||||
if u.String() != "" {
|
||||
return u.String(), true
|
||||
}
|
||||
}
|
||||
|
||||
return "", false
|
||||
}
|
||||
|
||||
return rawurl, true
|
||||
}
|
||||
|
||||
func linkable(elementName string) bool {
|
||||
switch elementName {
|
||||
case "a", "area", "blockquote", "img", "link", "script":
|
||||
return true
|
||||
default:
|
||||
return false
|
||||
}
|
||||
}
|
||||
@ -1,74 +0,0 @@
|
||||
// Copyright (c) 2014, David Kitchen <david@buro9.com>
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without
|
||||
// modification, are permitted provided that the following conditions are met:
|
||||
//
|
||||
// * Redistributions of source code must retain the above copyright notice, this
|
||||
// list of conditions and the following disclaimer.
|
||||
//
|
||||
// * Redistributions in binary form must reproduce the above copyright notice,
|
||||
// this list of conditions and the following disclaimer in the documentation
|
||||
// and/or other materials provided with the distribution.
|
||||
//
|
||||
// * Neither the name of the organisation (Microcosm) nor the names of its
|
||||
// contributors may be used to endorse or promote products derived from
|
||||
// this software without specific prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
|
||||
// AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
|
||||
// IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
|
||||
// DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
|
||||
// FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
|
||||
// DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
|
||||
// SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
|
||||
// CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
|
||||
// OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
|
||||
// OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
// +build go1.8
|
||||
|
||||
package bluemonday
|
||||
|
||||
import (
|
||||
"sync"
|
||||
"testing"
|
||||
)
|
||||
|
||||
func TestXSSGo18(t *testing.T) {
|
||||
|
||||
p := UGCPolicy()
|
||||
|
||||
tests := []test{
|
||||
{
|
||||
in: `<IMG SRC="jav
ascript:alert('XSS');">`,
|
||||
expected: ``,
|
||||
},
|
||||
{
|
||||
in: "<IMG SRC=`javascript:alert(\"RSnake says, 'XSS'\")`>",
|
||||
expected: ``,
|
||||
},
|
||||
}
|
||||
|
||||
// These tests are run concurrently to enable the race detector to pick up
|
||||
// potential issues
|
||||
wg := sync.WaitGroup{}
|
||||
wg.Add(len(tests))
|
||||
for ii, tt := range tests {
|
||||
go func(ii int, tt test) {
|
||||
out := p.Sanitize(tt.in)
|
||||
if out != tt.expected {
|
||||
t.Errorf(
|
||||
"test %d failed;\ninput : %s\noutput : %s\nexpected: %s",
|
||||
ii,
|
||||
tt.in,
|
||||
out,
|
||||
tt.expected,
|
||||
)
|
||||
}
|
||||
wg.Done()
|
||||
}(ii, tt)
|
||||
}
|
||||
wg.Wait()
|
||||
}
|
||||
Some files were not shown because too many files have changed in this diff Show More
Loading…
x
Reference in New Issue
Block a user